Monday, November 15, 2010
SANS 401 Security Essentials mentored by Doug Burks in Augusta GA
SANS 401 Security Essentials mentored by Doug Burks in Augusta GA
Why should you take SANS 401 Security Essentials?
* Considering the SANS Cyber Guardian program, SANS GSE (GIAC Security Expert) certification, or a Masters degree from the SANS Technical Institute? SANS 401 Security Essentials is required for each of these.
* Complement your CISSP. If you've already taken the CISSP, SANS 401 Security Essentials is the perfect technical complement. It takes all the theory that you learned at a high level for the CISSP and applies it in a very practical and updated manner. SANS 401 is "where the rubber meets the road".
* Are you a Systems Administrator or Network Engineer who would like to learn more about security? This course gives a very thorough overview of security theory and practice. Additionally, the tools and techniques that you learn in this class are directly applicable to your current job (and will prepare you for the future).
* Augment your Windows/Linux skills. Highly experienced with Windows, but not so much with Linux? Or the other way around? SANS 401 Security Essentials dedicates an entire section to Windows security and another entire section to Linux security.
These are just a few reasons to register for SANS 401 Security Essentials. For more information, please see:
SANS 401 Security Essentials mentored by Doug Burks in Augusta GA
Don't forget that ISSA members are eligible for a 25% discount! If you would like to register for the ISSA and/or SANS 401, please let me know and I'll be glad to help!
Wednesday, November 3, 2010
Security Onion: Intrusion Detection for your Network in Minutes
https://docs.google.com/present/edit?id=0ATQ65xrcMwNEZGZxMmp0ZnNfMTNnc3JzanpkYw&hl=en
Friday, October 29, 2010
Security Onion: Setup Script
Tuesday, October 19, 2010
Decoding Javascript Hex Encoding
Sunday, October 17, 2010
CISSP Resources: Cryptography
"CrypTool is a free, open-source e-learning application, used worldwide in the implementation and analysis of cryptographic algorithms. It supports both contemporary teaching methods at schools and universities as well as awareness training for employees and civil servants. "
-- http://www.cryptool.com/
Saturday, October 16, 2010
SSL Decryption using Tshark
Wednesday, October 13, 2010
CISSP Resources
Congratulations to the latest SANS GSEs!
Tuesday, October 12, 2010
Security Onion Live: 20101010 Edition!
The Security Onion LiveDVD is a bootable DVD that contains software used for installing, configuring, and testing Intrusion Detection Systems.
What software does it contain?
The Security Onion LiveDVD is based on Xubuntu 10.04 and contains Snort, Suricata, Sguil, Xplico, nmap, scapy, hping, netcat, tcpreplay, and many other security tools.
What can it be used for?
* The Security Onion LiveDVD can be used for Intrusion Detection. The Snort and Sguil daemons are automatically started on boot, listening on eth0 for any suspicious traffic and creating alerts in the Sguil database. Simply double-click the Sguil desktop shortcut to launch the GUI and view/investigate the alerts.
* The Security Onion LiveDVD can be used to test an Intrusion Detection System. Simply boot the DVD and use the included tools (such as nmap, scapy, hping, metasploit, and others) to test your existing IDS or to test the included Snort and Suricata IDS/IPS engines.
* The Security Onion LiveDVD can be used to install an Intrusion Detection System. Simply boot the DVD and double-click the Install desktop shortcut. For more information about installation, please see the "Installing to Hard Drive" section below.
System Requirements
512MB RAM is a minimum. 1GB or more is recommended.
Sguil
Here are the credentials to login to Sguil:
Username: sguil
Password: password
NOTE! It's "sguil" with a 'g', NOT a 'q'!
Disclaimer of Warranty
THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM .AS IS. WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
Limitation of Liability
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MODIFIES AND/OR CONVEYS THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
Installing to Hard Drive
You can use the Install shortcut on the Desktop to install Security Onion to your hard drive. Once you've completed the installation process and have rebooted into your new installation, you will want to:
* Install any available Ubuntu updates.
* Run the Setup desktop shortcut to:
Extra Packages installed from repositories
apache2.2-common argus-client argus-server autopsy bison bittwist build-essential chaosreader chkconfig chkrootkit cryptcat curl daemonlogger dcfldd ddrescue driftnet dsniff ettercap-gtk flawfinder flex foremost fwsnort ghex gpart gparted hping3 httptunnel hunt ifenslave-2.6 iisemulator inundator iptraf john labrea lame lfhex libapache2-mod-php5 libcap-ng-dev libcrypt-ssleay-perl libdumbnet-dev liblua5.1-0-dev libncurses5 libncurses5-dev libnet1-dev libnetfilter-queue-dev libnetfilter-queue1 libnfnetlink-dev libnfnetlink0 libnids-dev libpcap-dev libpcre3-dev libreadline6-dev libsqlite3-ruby libssl-dev libyaml-dev md5deep mtr mysql-server netsed netsniff-ng ngrep nmap ntp oinkmaster ophcrack ostinato p0f php5-cli php5-common php5-sqlite pkg-config pbnj pscan ptunnel python-all python-dev python-scapy rats recode remastersys ruby scanmem sdd sleuthkit sniffit sox splint ssdeep ssldump sslsniff sqlite steghide subversion tcl8.3 tcpick tcpreplay tcpslice tcpstat tcpxtract tct testdisk traceroute tshark udptunnel unhide uuid uuid-dev xtightvncviewer xprobe yersinia zenmap zlib1g-dev zenmap zlib1g-dev
Extra Packages installed from other sources
Snort
Suricata
Vortex IDS
Bro IDS
ABCIP
Dumbpig
NSMnow (includes Sguil, Barnyard2, Sancp, etc)
Xplico
Sunday, October 10, 2010
Greater Augusta ISSA 2010 Q4 Public Meeting: Doug Burks presents "Security Onion: Intrusion Detection for your Network in Minutes"
Please join us at the Greater Augusta ISSA Q4 meeting on Thursday, October 28. This is our last public meeting of 2010! I will be presenting "Security Onion: Intrusion Detection for your Network in Minutes". Security Onion is a project that I've been working on for the past few years. Its goal is to provide a pre-configured Intrusion Detection environment that can be downloaded for free and put to use in your network in less than an hour. It's based on Xubuntu 10.04 and contains Snort, Suricata, Sguil, Xplico, Vortex IDS, Bro IDS, Chaosreader, driftnet, hping3, scapy, Wireshark, and many other tools. Come see what Security Onion can do for you!
What: The Greater Augusta ISSA 2010 Q4 Public meeting: Doug Burks presents "Security Onion: Intrusion Detection for your Network in Minutes"
How: This is a FREE public meeting. Please confirm your reservation by sending an email to reservations@augusta.issa.org
When: Thursday October 28 9:00 - 11:00 AM
Where:
University Hall room 242
Augusta State University
2500 Walton Way
Augusta, GA 30904
http://www.aug.edu/public_relations/pr_map_campus.htm
On the morning of the presentation, don't forget to swing by the ASU Public Safety office to get a visitor pass for the parking lot. The Public Safety office is in the back corner of the campus. You can see it at the bottom-left of this map:
http://www.aug.edu/public_relations/asumap/images/PARKINGMAP1008PR.jpg
Speaker Bio
Doug Burks has over 10 years experience in Information Security. He has a Bachelor's degree in Computer Science and also holds the GSE, GPEN, GCIA Gold, GSEC, and CISSP certifications. Doug has worked in many organizations over the years, including government facilities, chemical plants, and the media industry. He excels at providing secure solutions for any environment using a budget of any size. Doug is the author of Security Onion Live (http://code.google.com/p/security-onion/ ), a free bootable DVD that contains many security tools. You can read more about Doug by visiting his blog athttp://securityonion.blogspot.com/.
Thursday, August 12, 2010
Suggestions for next version of Security Onion LiveCD
Monday, July 26, 2010
SANS MGT414: SANS(R) +S™ Training Program for the CISSP(R) Certification Exam in Augusta starts 10/12
Greater Augusta ISSA 2010 Q3 Public Meeting: Rob Lee presents the Mandiant M-Trends Report on APT (Advanced Persistent Threat)
The Greater Augusta ISSA is extremely excited to welcome Rob Lee this quarter! Rob Lee is the Curriculum Lead for Digital Forensic Training at the SANS Institute and is also a Director in MANDIANT’s Professional Services group. Please join us for this educational training opportunity.
What: The Greater Augusta ISSA 2010 Q3 Public meeting: Rob Lee presents the Mandiant M-Trends Report on APT (Advanced Persistent Threat)
How: This is a FREE public meeting. Please confirm your reservation by sending an email to reservations@augusta.issa.org
When: Thursday August 12 9:00 AM - 11:00 AM
Where:
University Hall Room UH-170
Augusta State University
2500 Walton Way
Augusta, GA 30904
http://www.aug.edu/public_relations/pr_map_campus.htm
On the morning of the presentation, don't forget to swing by the ASU Public Safety office to get a visitor pass for the parking lot. The Public Safety office is in the back corner of the campus. You can see it at the bottom-left of this map:
http://www.aug.edu/public_relations/asumap/images/PARKINGMAP1008PR.jpg
State of the Hack: M-Trends- The Advanced Persistent Threat
In early 2010, MANDIANT released its inaugural M-Trends report. This first report focused on our years of experience responding to computer security incidents perpetrated by the Advanced Persistent Threat (APT). The "straight from the battlefield" presentation provides case studies detailing the most recent computer security incidents MANDIANT has responded to involving the APT. During this presentation we detail the main points of the report through anonymous, in-depth case studies of attacks against commercial, government, and defense industrial base organizations. We demonstrate how the attackers gain access, how they behave once inside the victim network and the impact on the organizations. And, because understanding the problem is only half the battle, we wrap up with remediation recommendations that really work.
Robert Lee
Rob Lee is a Director in MANDIANT’s Professional Services group. Mr. Lee has more than 14 years of experience in computer forensics, vulnerability and exploit discovery, intrusion detection/prevention, and incident response. He served in the U.S. Air Force as a founding member of the 609th Information Warfare Squadron, the first U.S. military operational unit focused on information operations. Later, he was a member of the Air Force Office of Special Investigations where he conducted computer crime investigations, incident response, and computer forensics. Prior to joining MANDIANT, Mr. Lee worked directly with a variety of government agencies in the law enforcement, U.S. Department of Defense, and intelligence communities as the technical lead for a vulnerability discovery and exploit development team, lead for a cyber forensics branch, and lead for a computer forensic and security software development team. A graduate of the U.S. Air Force Academy, Mr. Lee also holds a Masters in Business Administration from Georgetown University. In 2009 he was awarded the Digital Forensic Examiner of the Year from the Forensic 4Cast Awards. Mr. Lee is co-author of the bestselling book Know Your Enemy, (2nd Edition). He is also a co-author of MANDIANT’s Threat intelligence report - M-Trends: The Advanced Persistent Threat.
Friday, June 18, 2010
SANS 560 Network Penetration Testing and Ethical Hacking -- Free Preview!
What: The Greater Augusta ISSA presents a SANS 560 Preview
How: This is a FREE public meeting. Please confirm your reservation by sending an email to reservations@augusta.issa.org
When: Thursday, July 15 9:00 AM - 11:00 AM
Where:
Augusta State University
2500 Walton Way
Augusta, GA 30904
Allgood Hall E-258
Please click here for directions to campus:
http://www.aug.edu/public_
On the morning of the presentation, don't forget to swing by the ASU Public Safety office to get a visitor pass for the parking lot. The Public Safety office is in the back corner of the campus. You can see it at the bottom-left of this map:
http://www.aug.edu/public_
Friday, May 28, 2010
SANS 560 Network Penetration Testing and Ethical Hacking in Augusta starts 8/17
- Do you perform penetration testing?
- Do you procure penetration testing?
- Do you manage penetration testers?
- Did you take SANS 504 and really enjoy the Hacker Techniques portion?
- Do you want to know more about how the bad guys perform recon, scan for vulnerabilities, perform exploitation, gain command execution, and then pivot further into the target environment?
Monday, April 19, 2010
Grepping an Active Log File and Mailing Matches
tail -n0 -f /var/log/secure | grep --line-buffered "user" | while read line; do echo $line | mail myemail@example.com -s "Found"; done
- adding multiple grep criteria
- modifying format of log entry to be emailed
- changing final action from email to something else (like adding an IPTables drop rule)
Thursday, April 8, 2010
Keep All Your Windows Software Updated with Secunia PSI
Tuesday, February 9, 2010
Defense in Depth using OSSEC and other free tools
- Suhosin (PHP Hardening)
- GreenSQL (Database firewall)
- Daemonlogger (full packet capture for forensics purposes)
- Others?
Friday, February 5, 2010
Solutions for CSAW Exercises for a burgeoning Army of Ninjas
Tuesday, February 2, 2010
Help Kill Adobe Flash - Enable HTML5 in Youtube
Friday, January 8, 2010
Computer Security Training
Sunday, September 6, 2009
Install Sguil on Fedora/RHEL/CentOS using NSMnow
You can read more at the SecurixLive site:
Install Sguil on Fedora/RHEL/CentOS using NSMnow
Tuesday, August 25, 2009
SANS 401 Mentor class coming to Augusta!
SANS 401 Security Essentials mentored by Doug Burks in Augusta GA
Why should you take SANS 401 Security Essentials?
* Are you a Systems Administrator or Network Engineer who would like to learn more about security? This course gives a very thorough overview of security theory and practice. Additionally, the tools and techniques that you learn in this class are directly applicable to your current job (and will prepare you for the future).
* DoD 8570 Compliance. If you work for the Department of Defense (or would like to), DoD Mandate 8570 requires security certification for any employee performing Information Assurance (security) work. The Security Essentials certification is among those required for 8570. For more information, please see the SANS 8570 page.
* Complement your CISSP. If you've already taken the CISSP, SANS 401 Security Essentials is the perfect technical complement. It takes all the theory that you learned at a high level for the CISSP and applies it in a very practical and updated manner. SANS 401 is "where the rubber meets the road".
* Augment your Windows/Linux skills. Highly experienced with Windows, but not so much with Linux? Or the other way around? SANS 401 Security Essentials dedicates an entire section to Windows security and another entire section to Linux security.
* Considering the SANS GSE (GIAC Security Expert) or SANS Masters program? SANS 401 Security Essentials is required for both.
These are just a few reasons to register for SANS 401 Security Essentials. For more information, please see:
SANS 401 Security Essentials mentored by Doug Burks in Augusta GA
Don't forget that ISSA members are eligible for a 25% discount! If you would like to register for the ISSA and/or SANS 401, please let me know and I'll be glad to help get you registered.
Sunday, August 16, 2009
Security Onion on Google Code and Google Groups
Security Onion on Google Code
Security Onion Wiki
Security Onion Issue Tracker
Security Onion Mailing List
Please take a look and let me know what you think!
Monday, August 3, 2009
Security Onion LiveCD 20090731
2009/07/31: New Release!
* All Xubuntu 9.04 updates as of 2009/07/31.
* Added sqlite and libsqlite3-ruby packages for db_autopwn.
* Added fwbuilder.
* Latest Metasploit msf v3.3-dev as of 2009/07/31.
* Latest Nmap 5.05BETA1 as of 2009/07/31.
The Security Onion LiveCD can be downloaded from the following location:
http://distro.ibiblio.org/pub/
Please let me know if you have any questions or suggestions.
Wednesday, July 29, 2009
Using Metasploit's db_autopwn on the Security Onion LiveCD
I was testing the new Security Onion LiveCD yesterday and trying to use Metasploit's db_autopwn function. The first step of db_autopwn is to create a database to hold the information about your potential targets. This is done with the db_create command. When I issued this command, I got an error about sqlite3 (the default database driver for db_autopwn).
I had forgotten to install the sqlite and libsqlite3-ruby packages. If you're having this problem, you can fix it with the following command:
sudo aptitude -y install sqlite libsqlite3-ruby
This will be fixed in the next release of the Security Onion LiveCD.
securityonion@securityonion:/usr/local/bin/framework3$ ./msfconsole
=[ msf v3.3-dev
+ -- --=[ 392 exploits - 234 payloads
+ -- --=[ 20 encoders - 7 nops
=[ 168 aux
msf > db_create
[*] Creating a new database instance...
[-] Error while running command db_create: no such file to load -- sqlite3
msf > quit
securityonion@securityonion:/usr/local/bin/framework3$ sudo aptitude -y install sqlite libsqlite3-ruby
Reading package lists... Done
Building dependency tree
Reading state information... Done
Reading extended state information
Initializing package states... Done
The following NEW packages will be installed:
libsqlite0{a} libsqlite3-ruby libsqlite3-ruby1.8{a} sqlite
0 packages upgraded, 4 newly installed, 0 to remove and 0 not upgraded.
Need to get 247kB of archives. After unpacking 811kB will be used.
Writing extended state information... Done
Get:1 http://archive.ubuntu.com jaunty/main libsqlite0 2.8.17-4build1 [176kB]
Get:2 http://archive.ubuntu.com jaunty/universe libsqlite3-ruby1.8 1.2.4-2 [51.3kB]
Get:3 http://archive.ubuntu.com jaunty/universe libsqlite3-ruby 1.2.4-2 [4042B]
Get:4 http://archive.ubuntu.com jaunty/main sqlite 2.8.17-4build1 [16.2kB]
Fetched 247kB in 1s (150kB/s)
Selecting previously deselected package libsqlite0.
(Reading database ... 118520 files and directories currently installed.)
Unpacking libsqlite0 (from .../libsqlite0_2.8.17-4build1_i386.deb) ...
Selecting previously deselected package libsqlite3-ruby1.8.
Unpacking libsqlite3-ruby1.8 (from .../libsqlite3-ruby1.8_1.2.4-2_i386.deb) ...
Selecting previously deselected package libsqlite3-ruby.
Unpacking libsqlite3-ruby (from .../libsqlite3-ruby_1.2.4-2_all.deb) ...
Selecting previously deselected package sqlite.
Unpacking sqlite (from .../sqlite_2.8.17-4build1_i386.deb) ...
Processing triggers for man-db ...
Setting up libsqlite0 (2.8.17-4build1) ...
Setting up libsqlite3-ruby1.8 (1.2.4-2) ...
Setting up libsqlite3-ruby (1.2.4-2) ...
Setting up sqlite (2.8.17-4build1) ...
Processing triggers for libc6 ...
ldconfig deferred processing now taking place
Reading package lists... Done
Building dependency tree
Reading state information... Done
Reading extended state information
Initializing package states... Done
Writing extended state information... Done
securityonion@securityonion:/usr/local/bin/framework3$ ./msfconsole
=[ msf v3.3-dev
+ -- --=[ 392 exploits - 234 payloads
+ -- --=[ 20 encoders - 7 nops
=[ 168 aux
msf > db_create
[*] Creating a new database instance...
[*] Successfully connected to the database
[*] File: /home/securityonion/.msf3/sqlite3.db
msf >
Tuesday, July 28, 2009
Security Onion LiveCD 20090724
* All Xubuntu 9.04 updates as of 2009/07/24.
* Added a Security Onion section to the Applications menu.
* Latest Metasploit msf v3.3-dev as of 2009/07/24.
* Latest Nmap as of 2009/07/24.
The Security Onion LiveCD can be downloaded from the following location:
http://distro.ibiblio.org/pub/
Please let me know if you have any questions or suggestions.
Saturday, July 11, 2009
Know Thy ISP
"Investigators may not yet know who was behind a series of cyberattacks on the U.S. and South Korea, but analysts are getting a better grasp on where the nations' governments may have gone wrong. Numerous government Web sites in both countries have been hit by distributed denial-of-service attacks, starting on the Fourth of July and continuing into today. Dozens of high-profile sites have been targeted, including those of the Federal Trade Commission, the Department of Treasury, and other major federal agencies."Quote of the day:
"'Too many federal agency security people did not know which network service provider connected their Web sites to the Internet,' explains Alan Paller, director of research at the SANS Institute, a security research organization."Alan's statement is quite scary, but I'm sure quite true. When the killer clowns come knocking at your firewall's door, you need to be able to pull the plug in a hurry. Perhaps we should have Internet fire drills where we propose a mock DDoS attack and have our technicians play out the scenario. Who ya gonna call?
Friday, July 10, 2009
SANS Courses for the US-CERT GFIRST conference in August
"In August, SANS will be running 5 tracks in support of the US-CERT GFIRST conference taking place at the Omni Hotel at CNN Center (http://www.us-cert.gov/GFIRST/). SANS is pleased to present the following course offerings:
Security 501: Advanced Security Essentials - Enterprise Defender
http://www.sans.org/atlanta09/description.php?tid=2722
August 17-22
Security 504: Hacker Techniques, Exploits & Incident Handling
http://www.sans.org/atlanta09/description.php?tid=243
August 17-22
Security 441: Windows Forensics
http://www.sans.org/atlanta09/description.php?tid=3012
August 27-28
Security 553: Metasploit for Penetration Testers
http://www.sans.org/atlanta09/description.php?tid=3022
August 27
Security 517: Cutting-Edge Hacking Techniques
http://www.sans.org/atlanta09/description.php?tid=1927
August 28
This will be the first time we are offering Security 501 and a rare opportunity to take this course from Dr. Eric Cole in a small class setting. We are also offering 3 short courses which offer a great opportunity to get SANS content in only 1 or 2 days."
Tuesday, June 30, 2009
Suggestions for the Security Onion LiveCD
Tuesday, June 16, 2009
Security Onion LiveCD 20090613
-All Xubuntu 9.04 updates as of 2009/06/13.
-Added JJ Cummings's pulledpork as an alternative to oinkmaster. All pulledpork files are in:
/usr/local/bin/pulledpork/
-Added Leon Ward's dumbpig for checking custom Snort rules:
/usr/local/bin/dumbpig.pl
-Added Bro IDS for Marcus J. Carey. All Bro files are in:
/usr/local/bro/
The Security Onion LiveCD can be downloaded from the following location:
http://distro.ibiblio.org/pub/
UPDATE: Some ibiblio mirrors are showing an index page which contains no links. Here are the direct links to the ISO and MD5 file:
http://distro.ibiblio.org/pub/linux/distributions/security-onion/security-onion-livecd-20090613.iso
http://distro.ibiblio.org/pub/linux/distributions/security-onion/security-onion-livecd-20090613.md5
Thursday, June 4, 2009
The Security Onion LiveCD is now available!
http://distro.ibiblio.org/pub/
What is it?
The Security Onion LiveCD is a bootable CD that contains software used for installing, configuring, and testing Intrusion Detection Systems.
What software does it contain?
The Security Onion LiveCD is based on Xubuntu 9.04 and contains Snort 2.8.4.1, Snort 3.0.0b3 (Beta), sguil, idswakeup, nmap, metasploit, scapy, hping, fragroute, fragrouter, netcat, paketto, tcpreplay, and many other security tools.
What can it be used for?
- The Security Onion LiveCD can be used for Intrusion Detection. Simply boot the CD and double-click either the Snort-Sguil or SnortSP-Sguil desktop shortcuts. The Snort and Sguil daemons will then start, listening on eth0 for any suspicious traffic and creating alerts in the Sguil console.
- The Security Onion LiveCD can be used to test an Intrusion Detection System. Simply boot the CD and use the included tools (such as nmap, metasploit, idswakeup, scapy, hping, and others) to test your existing IDS or to test the included Snort 2.8.4.1 and Snort 3.0 Beta 3.
- The Security Onion LiveCD can be used to install an Intrusion Detection System. Simply boot the CD and double-click the Install desktop shortcut. For more information about installation, please see the README desktop shortcut.
Please take a look at the Security Onion LiveCD and let me know what you think!
* Special thanks to:
- Marty Roesch and the whole SourceFire team for all of their work these last 10 years to get Snort to where it is today.
- The Sguil team for the best open-source tool to manage Snort alerts.
- The SecurixLive crew for their awesome NSMnow installer, the easiest way to install and configure Snort/Sguil on Ubuntu Linux.
- Ubuntu (and Debian) for their well-made Linux distribution(s).
- The Reconstructor team for a very easy to use tool for remastering Ubuntu LiveCDs.
- All developers in the open-source community who work so hard and produce such amazing tools.
Thursday, May 7, 2009
Sguil on Ubuntu 9.04 in 3 Steps using NSMnow
Disclaimer: I offer no warranties of any kind. If your box breaks, you get to keep both pieces!
Step 1: Get root privileges
##########################Step 2: Install NSMnow
sudo -i
##########################
##########################Step 3: Configure AppArmor and start NSMnow
mkdir /usr/local/src/NSMnow
cd /usr/local/src/NSMnow
wget http://www.securixlive.com/download/nsmnow/NSMnow-1.4.0.tar.gz
tar zxvf NSMnow-1.4.0.tar.gz
./NSMnow -i -y
##########################
##########################Snort is now capturing packets on eth0 and analyzing them. Let's verify that now.
if ! grep "/nsm/server_data/server1/load" /etc/apparmor.d/usr.sbin.mysqld > /dev/null
then
# Remove the last line of the file (a single right curly brace)
sed -i '$d' /etc/apparmor.d/usr.sbin.mysqld
# Add a line that allows MySQL to read the load directory
echo " /nsm/server_data/server1/load/* r," >> /etc/apparmor.d/usr.sbin.mysqld
# Append the right curly brace to end the file
echo "}" >> /etc/apparmor.d/usr.sbin.mysqld
fi
if ! grep "/nsm/sensor_data/sensor1/dailylogs" /etc/apparmor.d/usr.sbin.tcpdump > /dev/null
then
# Remove the last line of the file (a single right curly brace)
sed -i '$d' /etc/apparmor.d/usr.sbin.tcpdump
# Add a line that allows tcpdump to read all dailylogs
echo " /nsm/sensor_data/sensor1/dailylogs/**[^/] r," >> /etc/apparmor.d/usr.sbin.tcpdump
echo "}" >> /etc/apparmor.d/usr.sbin.tcpdump
fi
/etc/init.d/apparmor restart
/usr/local/sbin/nsm --all --start
##########################
Launch the Sguil client by opening a new terminal and typing the following:
##########################When prompted, login to Sguil using the default credentials:
sguil.tk
##########################
Username: sguil
Password: password
Next, create some alerts by opening a browser and going to:
http://www.testmyids.com
Finally, go into the Sguil console and you should see two new alerts:
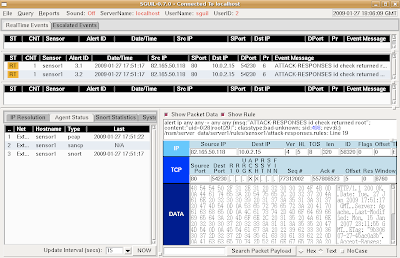
This demonstrates that Snort is analyzing packets and outputting in unified2 format, which is then read by Barnyard2 and inserted into the Sguil database.
When finished, close the Sguil window and return to your NSMnow window. Then type the following to terminate all NSMnow processes:
/usr/local/sbin/nsm --all --stop
Search This Blog
Featured Post
Quick Malware Analysis: NETSUPPORT RAT pcap from 2025-08-20
Thanks to Brad Duncan for sharing this pcap from 2025-08-20 on his malware traffic analysis site! Due to issues with Google flagging a warni...
Popular Posts
-
Introduction Recent events have forced us to change course on the base operating system (OS) for Security Onion 2.4. On 6/21/2023, Red Hat ...
-
Hurricane Helene Update On Friday, September 27, Hurricane Helene hit Augusta GA. All of our team members are safe, but many folks had signi...
-
Introduction Jeffrey Medsger reported several command injection and SQL injection vulnerabilities in Squert. Wes Lambert also discovered s...
Blog Archive
- August 2025 (4)
- July 2025 (3)
- June 2025 (3)
- May 2025 (5)
- April 2025 (2)
- March 2025 (7)
- February 2025 (5)
- January 2025 (11)
- December 2024 (3)
- November 2024 (1)
- October 2024 (9)
- September 2024 (16)
- August 2024 (3)
- July 2024 (7)
- June 2024 (5)
- May 2024 (2)
- April 2024 (7)
- March 2024 (5)
- February 2024 (3)
- January 2024 (3)
- December 2023 (15)
- November 2023 (27)
- October 2023 (18)
- September 2023 (3)
- August 2023 (8)
- July 2023 (4)
- June 2023 (3)
- May 2023 (2)
- April 2023 (4)
- March 2023 (4)
- February 2023 (5)
- January 2023 (3)
- December 2022 (5)
- November 2022 (2)
- October 2022 (9)
- September 2022 (3)
- August 2022 (8)
- July 2022 (7)
- June 2022 (9)
- May 2022 (14)
- April 2022 (7)
- March 2022 (6)
- February 2022 (11)
- January 2022 (12)
- December 2021 (19)
- November 2021 (25)
- October 2021 (22)
- September 2021 (23)
- August 2021 (30)
- July 2021 (13)
- June 2021 (4)
- May 2021 (3)
- April 2021 (4)
- March 2021 (7)
- February 2021 (5)
- January 2021 (4)
- December 2020 (13)
- November 2020 (5)
- October 2020 (12)
- September 2020 (3)
- August 2020 (6)
- July 2020 (8)
- June 2020 (5)
- May 2020 (9)
- April 2020 (11)
- March 2020 (7)
- February 2020 (4)
- January 2020 (1)
- December 2019 (6)
- November 2019 (4)
- October 2019 (8)
- September 2019 (7)
- August 2019 (7)
- July 2019 (4)
- June 2019 (7)
- May 2019 (20)
- April 2019 (8)
- March 2019 (7)
- February 2019 (7)
- January 2019 (12)
- December 2018 (12)
- November 2018 (13)
- October 2018 (10)
- September 2018 (4)
- August 2018 (16)
- July 2018 (11)
- June 2018 (13)
- May 2018 (4)
- April 2018 (11)
- March 2018 (9)
- February 2018 (10)
- January 2018 (9)
- December 2017 (7)
- November 2017 (7)
- October 2017 (9)
- September 2017 (4)
- August 2017 (7)
- July 2017 (5)
- June 2017 (8)
- May 2017 (4)
- April 2017 (2)
- March 2017 (1)
- February 2017 (3)
- January 2017 (15)
- December 2016 (9)
- November 2016 (3)
- October 2016 (5)
- September 2016 (13)
- August 2016 (12)
- July 2016 (10)
- June 2016 (7)
- May 2016 (7)
- April 2016 (7)
- March 2016 (10)
- February 2016 (13)
- January 2016 (10)
- December 2015 (1)
- November 2015 (1)
- October 2015 (3)
- September 2015 (5)
- August 2015 (7)
- July 2015 (7)
- June 2015 (12)
- May 2015 (6)
- April 2015 (6)
- March 2015 (6)
- February 2015 (10)
- January 2015 (11)
- December 2014 (5)
- November 2014 (3)
- October 2014 (6)
- September 2014 (20)
- August 2014 (7)
- July 2014 (10)
- June 2014 (10)
- May 2014 (3)
- April 2014 (9)
- March 2014 (6)
- February 2014 (9)
- January 2014 (8)
- December 2013 (5)
- November 2013 (2)
- October 2013 (7)
- September 2013 (5)
- August 2013 (7)
- July 2013 (9)
- June 2013 (7)
- May 2013 (11)
- April 2013 (3)
- March 2013 (3)
- February 2013 (3)
- January 2013 (3)
- December 2012 (3)
- November 2012 (1)
- October 2012 (1)
- September 2012 (1)
- August 2012 (2)
- May 2012 (4)
- April 2012 (6)
- March 2012 (8)
- February 2012 (4)
- January 2012 (13)
- December 2011 (9)
- November 2011 (8)
- October 2011 (8)
- September 2011 (8)
- July 2011 (4)
- June 2011 (5)
- May 2011 (2)
- April 2011 (1)
- February 2011 (1)
- January 2011 (11)
- November 2010 (4)
- October 2010 (8)
- August 2010 (1)
- July 2010 (2)
- June 2010 (1)
- May 2010 (1)
- April 2010 (2)
- February 2010 (3)
- January 2010 (1)
- September 2009 (1)
- August 2009 (3)
- July 2009 (4)
- June 2009 (3)
- May 2009 (1)
- April 2009 (8)
- February 2009 (1)
- January 2009 (9)
- November 2008 (2)
- October 2008 (4)
- September 2008 (3)