About the Course
"I started Security Onion in 2008 to provide a comprehensive platform for intrusion detection, network security monitoring, and log management. Today, Security Onion has over 775,000 downloads and is being used by organizations around the world to help monitor and defend their networks. This class is the culmination of years of lessons learned while building Security Onion and best practices developed while deploying Security Onion to real networks and doing real incident response with it."
-- Doug Burks
What do previous students say about the class?
"I highly, HIGHLY recommend attending this class. I attended the class in Houston and it was excellent ... I also met many interesting people and made some new contacts. All in all, if this class comes anywhere near me again ... I'll be going if I have to host a bake sale to get there."
"I appreciated the mixture of Doug's obvious significant real world experience, paired with his deep knowledge of security onion. I felt like the class not only helped me understand the tools but also helped me understand how I might best apply those tools."
"One of the best courses I have taken. Phil was extremely knowledgeable. I would recommend this class to other people."
What do students get?
- 4 days of classroom instruction from the developers of Security Onion
- over 200 pages of course material
- Certificate of Completion
- FREE Admission to Security Onion Conference on October 4, 2019
- FREE Admission to BSidesAugusta on October 5, 2019
- Validated parking pass at the Georgia Cyber Center parking deck for each day of class
- Bottled Water All Day
- Morning Coffee
When is the class?
Monday, September 30, 2019 through Thursday, October 3, 2019
8:00 AM - 5:00 PM (Eastern Time) each day
When does registration close?
Registration closes Monday, September 23, at 11:59 PM Eastern.
Where is the class being held?
The class will be held at the Georgia Cyber Center Hull McKnight Building, 100 Grace Hopper Lane, Augusta, GA 30901
 |
| Georgia Cyber Center |
The GCC is walking distance from the BSidesAugusta preferred hotel. If you are driving, there is a paid parking deck onsite. Validated parking is included with the price of registration.
What hardware will be required for the class?
Students must bring their own laptop that meets the following requirements:
- At least 12-16 GB RAM on the machine, so that a full 8 GB RAM that can be dedicated to one virtual machine (VM). More is better.
- At least 4 total CPU cores on the machine, so that 2 cores can be dedicated to one VM. More is better.
- One internal hard drive should have at least 50 GB free disk space. More is better. Solid State Drives are preferred, but not required.
- Virtualization software must be installed. We recommend VMWare Workstation, Workstation Player, or Fusion. Oracle VirtualBox works also. Please, no ESXi or similar platforms. Each student machine will only run one VM, which students install in class from the Security Onion ISO image. The VM will not interconnect with VMs on other student machines.
- The hardware and operating system must be capable of running a 64 bit VM. Note: Some 64 bit machines don't automatically support a 64 bit VM. This should be tested ahead of class. See https://securityonion.net/docs/installation
- Students need administrator/root access to the host operating system on the student machine. They should need this only once to add a virtual sniffing NIC to the VM.
- Must have an adequately sized screen. Note: Tablet computers such as the Microsoft Surface usually do not meet this requirement.
- Must be able to connect to a wireless network for Internet access.
Which version of Security Onion will we be using?
We'll be using the latest Security Onion version as of September 9, 2019.
The latest release can be found here:
https://securityonion.net/download
What do students need to bring to class?
Students need to bring the following:
- A laptop meeting the requirements described above
- State-issued ID or Passport
- Eventbrite ticket for this event
What skills/knowledge should students have before attending this course?
Students should have a basic understanding of networks, TCP/IP, and standard protocols such as DNS, HTTP, etc. Some Linux knowledge/experience is recommended, but not required.
What's the cancellation policy?
BSidesAugusta and Security Onion Solutions reserve the right to cancel this class up to one day after registration closes if the class does not meet a minimum number of students. If class is cancelled, the training ticket cost will be refunded. Contact BSidesAugusta through their registration page for more information.
What's the refund policy?
You may request a training refund for training purchased through this site (for the cost of the training only) through 9/23/2019. Contact BSidesAugusta through their registration page for more information.
Are there discounts available?
We offer discounts for members of ISSA and Infragard. Contact us for more information.
Anything else going on in Augusta that week?
Yes! Students enrolled in the Augusta Security Onion Basic Course class gain free admission to:
- Security Onion Conference on Friday, October 4, 2019, at the GCC (same building as the class)
- BSidesAugusta on Saturday, October 5, 2019 at the Augusta University Harrison Education Commons
How do I register for this class?
BSidesAugusta is hosting the registration for this training:
https://bsidesaugusta2019.eventbrite.com
Are there any special rates at nearby hotels?
Yes! See the BSidesAugusta website for hotel details:
https://bsidesaugusta.org/reserve-hotel
What topics are covered in this class?
- Network Security Monitoring (NSM) methodology
- Security Onion Installation
- Configuration
- Setup Phase 1 - Network configuration
- Setup Phase 2 - Service configuration
- Evaluation Mode vs Production Mode
- Verifying services
- Analyzing Alerts
- Replaying traffic
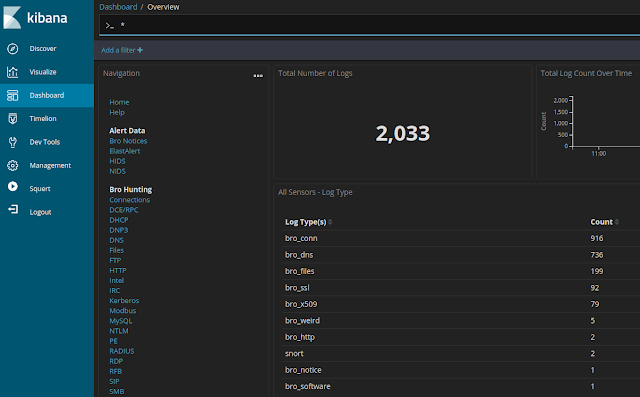
- Squert
- Sguil
- Kibana
- Hunting with Kibana
- Create custom dashboards in Kibana
- Pivoting between interfaces
- Pivoting to full packet capture
- Bro
- Introduction
- Bro Programming Language
- Bro-IDS
- Bro Logs
- Bro Scripts
- Bro Intel Framework
- Production Deployment
- Advanced Setup
- Master vs sensor
- Node types - Master, Forward, Heavy, Storage
- Command line setup with sosetup.conf
- Architectural recommendations
- Sensor placement
- Hardening
- Administration
- Maintenance
- Tuning
- Using PulledPork to disable rules
- BPFs to filter traffic
- Spinning up additional Snort/Suricata/Bro workers to handle higher traffic loads
- Case Studies
- 1-2 Case Studies on Day 1
- 1-2 Case Studies on Day 2
- 2-4 Case Studies on Day 3
- 3-4 Case Studies on Day 4
- Wrap-up/Q&A
Class registration is hosted by BSidesAugusta, so to register please see:
https://bsidesaugusta2019.eventbrite.com
For other training options, please see:
https://securityonionsolutions.com
Hope to see you there!