Thanks to Brad Duncan for sharing this pcap from 2023-07-25 on his malware traffic analysis site! Google currently has a warning for the site, so we're not including the actual hyperlink but it should be easy to find.
We did a quick analysis of this pcap on the NEW Security Onion 2.4. If you'd like to follow along, you can do the following:
- install Security Onion 2.4 in a VM:
https://docs.securityonion.net/en/2.4/first-time-users.html - import the pcap using so-import-pcap:
https://docs.securityonion.net/en/2.4/so-import-pcap.html#so-import-pcap - optionally enable the new DNS lookups feature:
https://docs.securityonion.net/en/2.4/soc-customization.html?#reverse-dns-lookups
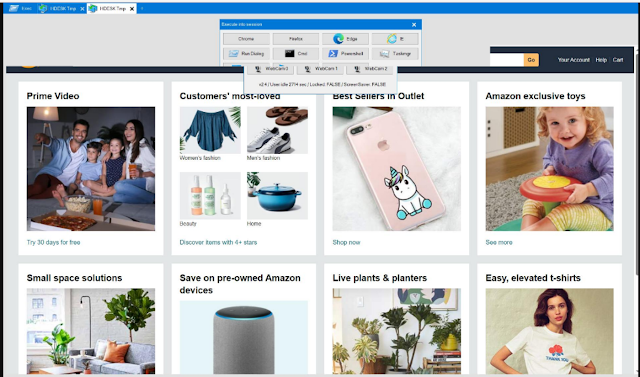
The screenshots at the bottom of this post show some of the interesting alerts, metadata logs, and session transcripts. Want more practice? Check out our other Quick Malware Analysis posts at:
https://blog.securityonion.net/search/label/quick%20malware%20analysis
About Security Onion
Security Onion is a versatile and scalable platform that can run on small virtual machines and can also scale up to the opposite end of the hardware spectrum to take advantage of extremely powerful server-class machines. Security Onion can also scale horizontally, growing from a standalone single-machine deployment to a full distributed deployment with tens or hundreds of machines as dictated by your enterprise visibility needs. To learn more about Security Onion, please see:
https://securityonion.net
Do you want to deploy the new Security Onion 2.4 to your enterprise but need training? We just announced a new class with 10% discount:
https://blog.securityonion.net/2023/12/10-early-bird-discount-for-security.html
Do you want to deploy Security Onion to your enterprise and want the best enterprise hardware? Here are the top 5 reasons to purchase appliances from Security Onion Solutions: https://blog.securityonion.net/2023/08/top-5-reasons-to-purchase-security.html
Screenshots
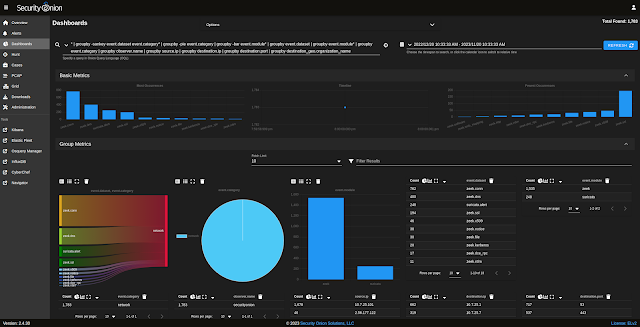
First, we start with the overview of all alerts and logs:



















No comments:
Post a Comment