I've updated the securityonion-bro-scripts package to include Seth Hall's ShellShock detector from here:
https://github.com/broala/bro-shellshock
securityonion-bro-scripts also creates a new directory called /opt/bro/share/bro/intel/ that makes it easy for you to add intel to the Bro Intel framework.
Mike Reeves, Ryan Peck, and I have updated the OnionSalt scripts to replicate more data from master to sensor. This includes the /opt/bro/share/bro/intel/ directory mentioned above and also OSSEC's agent.conf and local_decoder.xml files.
Finally, SaltStack has updated their salt packages, so we include that as well.
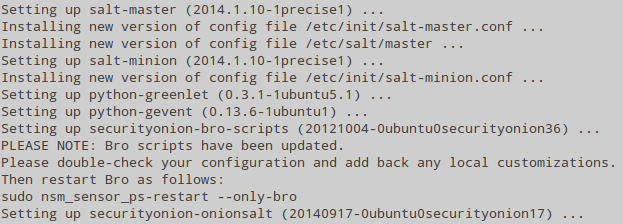
New package versions:
salt - 2014.1.10-1precise1
securityonion-bro-scripts - 20121004-0ubuntu0securityonion36
securityonion-onionsalt - 20140917-0ubuntu0securityonion17
These new packages have been tested by the following (thanks!):
Brian Kellogg
Rob C
Issues Resolved:
Issue 612: securityonion-bro-scripts: include ShellShock detection
https://code.google.com/p/security-onion/issues/detail?id=612
Issue 606: securityonion-bro-scripts: create /opt/bro/share/bro/intel/
with example intel
https://code.google.com/p/security-onion/issues/detail?id=606
Issue 609: Onionsalt should copy /opt/bro/share/bro/intel/
https://code.google.com/p/security-onion/issues/detail?id=609
Issue 580: onionsalt should copy OSSEC agent.conf and local_decoder.xml
https://code.google.com/p/security-onion/issues/detail?id=580
Issue 579: Update salt
https://code.google.com/p/security-onion/issues/detail?id=579
Updating
The new packages are now available in our stable repo. Please see the following page for full update instructions:
https://code.google.com/p/security-onion/wiki/Upgrade
To apply the new Bro ShellShock detection, you'll need to restart Bro as follows:
sudo nsm_sensor_ps-restart --only-bro
Screenshots
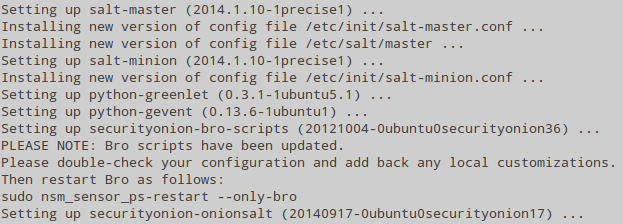 |
| Update Process |
 |
| Restarting Bro to load new ShellShock Detection |
 |
| /opt/bro/share/bro/ now contains intel/ and shellshock/ directories |
 |
| Bro ShellShock logs (http.log and notice.log) |
Feedback
If you have any questions or problems, please use our security-onion mailing list:
https://code.google.com/p/security-onion/wiki/MailingLists
Training
Only 17 seats left for the 3-day Security Onion class in Richmond VA!
https://security-onion-class-20141020.eventbrite.com/
Commercial Support
Need commercial support? Please see:
http://securityonionsolutions.com
Help Wanted
If you and/or your organization have found value in Security Onion, please consider giving back to the community by joining one of our teams:
https://code.google.com/p/security-onion/wiki/TeamMembers
We especially need help in answering support questions on the mailing list:
http://groups.google.com/group/security-onion
We also need help testing new packages:
http://groups.google.com/group/security-onion-testing
Thanks!