Security Onion 2.4.70 is now available! It includes some new features for our fellow defenders including our new Detections interface to help you take your detection engineering capabilities to the next level!
Security Onion is a cybersecurity platform built by defenders for defenders. For this release, we spent several MONTHS thinking through the defender workflow specifically around detection engineering. This resulted in a new interface called Detections that makes it super simple to tune your NIDS rules for Suricata, Sigma rules for ElastAlert, and YARA rules for Strelka.
We recently shared a sneak peek at Detections and you can find that video here:
https://youtu.be/oxR4q53N6OI
Since that sneak peak video, Detections has gotten even better!
Let's walk through the interface. First, we start with the main Detections page:
The upper-right corner shows a count of detections that matched the search query. To the left of that is a status indicator for each of the detection engines. The status can show whether a sync is in process, as well as whether the engine has detected errors. Clicking the status text will navigate to Hunt and attempt to find related logs.
The Detections menu option on the left side of the application will show an exclamation mark if there is a recent failure in any of the detection engines. In this situation the web browser tab will also show an exclamation indicator. If no failures are detected, and if any of the detection engines has an import pending or is performing a rule import, synchronization, or migration, then a blue hourglass will appear next to the Detections menu option.
The Options menu allows you to synchronize a particular detection engine such as ElastAlert, Strelka, or Suricata:
- The differential update is a lightweight sync that will skip the thorough sync and comparison of each individual rule. For example, with Suricata it will compute and compare the hash of the source rule list with the hash of the deployed rules, and only if there’s a mismatch will it perform the full sync.
- A full sync can involve inspecting and comparing individual rules, of which there can be thousands. This more thorough sync can take much longer than the differential sync. Note that each engine has its own unique synchronization process.
- click the Language drop-down and select your desired rule language
- optionally specify a license
- add the signature
- click the CREATE button and the detection should deploy to your grid at the next 15-minute cycle
Here's an example of a YARA rule:
As you can see, Detections will help you take your detection engineering capabilities to the next level!
SOC Dashboards
In addition to Detections, we spent a lot of time updating SOC Dashboards! We updated just about every one of our existing default dashboards to standardize on a new sankey diagram format that will help you see relationships between different fields more clearly and filter those fields more quickly. We also added column definitions for many different data types to aid you in your hunting expeditions. This release also includes a complete set of dashboards for Elastic Agent:
We also added new dashboards for NetFlow, Kismet, and more:
Elastic Integrations
This release adds a new Elastic integration for CEF. You can find our full list of supported Elastic integrations at:
https://docs.securityonion.net/en/2.4/third-party-integrations.htmlTelemetry
Starting in this release, Security Onion Console (SOC) can optionally send telemetry data to Google Analytics.
During setup, or during non-automated soup invocations, the user must choose to enable or disable SOC telemetry collection.
After installation, grid administrators can enable or disable SOC Telemetry via the configuration interface. Search for SOC Telemetry in the Configuration screen.
The purpose of this telemetry is to help the Security Onion development team improve the product. Specifically, by knowing which user-interface features are being used, and how the user interacts with the SOC user interface, the development team can better prioritize new features, improvements to the existing user interface, and begin deprecating features that are rarely used. Deprecating unused features will help developers avoid spending their time and effort maintaining and upgrading areas of the product that aren’t widely used. This allows more time to be spent on new features and bug fixes, directly benefiting Security Onion users.
For more information, please see the Telemetry section of the docs:
https://docs.securityonion.net/en/2.4/telemetry.html
Other Features and Fixes
There are many more features and fixes included in this release! For a complete list of all changes, please see the Release Notes:
https://docs.securityonion.net/en/2.4/release-notes.html#changes
Known Issues
For a list of known issues, please see:
https://docs.securityonion.net/en/2.4/release-notes.html#known-issues
About Security Onion
Security Onion is a free and open platform built by defenders for defenders. It includes network visibility, host visibility, intrusion detection honeypots, log management, and case management.
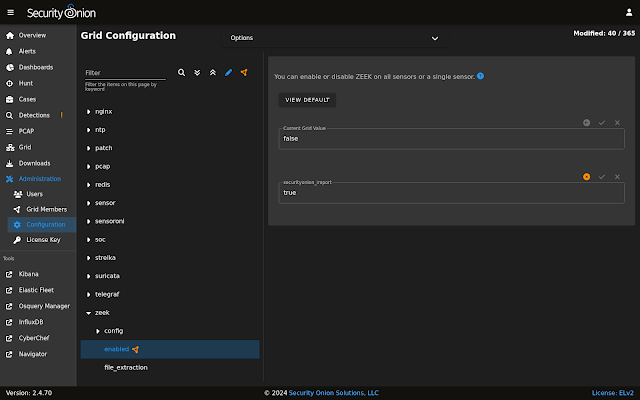
For network visibility, we offer signature based detection via Suricata, rich protocol metadata and file extraction using your choice of either Zeek or Suricata, full packet capture, and file analysis. For host visibility, we offer the Elastic Agent which provides data collection, live queries via osquery, and centralized management using Elastic Fleet. Intrusion detection honeypots based on OpenCanary can be added to your deployment for even more enterprise visibility. All of these logs flow into Elasticsearch and we’ve built our own user interfaces for alerts, dashboards, threat hunting, case management, and grid management.
Security Onion has been downloaded over 2 million times and is being used by security teams around the world to monitor and defend their enterprises. Our easy-to-use Setup wizard allows you to build a distributed grid for your enterprise in minutes!
Documentation
You can find our online documentation here:
https://docs.securityonion.net/en/2.4/
Documentation is always a work in progress. If you find documentation that needs to be updated, please let us know as described in the Feedback section below.
New Installations
If this is your first time installing Security Onion 2.4, then we highly recommend starting with an IMPORT installation as shown at:
https://docs.securityonion.net/en/2.4/first-time-users.html
Once you’re comfortable with your IMPORT installation, then you can move on to more advanced installations as shown at:
https://docs.securityonion.net/en/2.4/architecture.html
Existing 2.4 Installations
If you have an existing Security Onion 2.4 installation, you can update to the latest version using soup:
https://docs.securityonion.net/en/2.4/soup.html
Before updating your production deployment, we highly recommend testing the upgrade process on a test deployment that closely matches your production deployment if possible.
In preparation for the new Detections module, the following will be completed during soup:
- Playbook Plays will be backed up to /nsm/backup/detections-migration/ and any active Elastalert rules will be backed up and removed.
- Suricata tuning configurations will be backed to /nsm/backup/detections-migration/ and any thresholds will be migrated over to the new Detections module.
2.3 EOL
As a reminder, Security Onion 2.3 reached End Of Life (EOL) on April 6, 2024:
https://blog.securityonion.net/2023/10/6-month-eol-notice-for-security-onion-23.html
Thanks
Lots of love went into this release!
Special thanks to all our folks working so hard to make this release happen!
- Josh Brower
- Jason Ertel
- Wes Lambert
- Corey Ogburn
- Josh Patterson
- Mike Reeves
Questions, Problems, and Feedback
If you have any questions or problems relating to Security Onion 2.4, please use the 2.4 category at our Discussions site:
https://github.com/Security-Onion-Solutions/securityonion/discussions/categories/2-4
Training
Need training? Start with our free Security Onion Essentials training and then take a look at some of our other official Security Onion training!
https://securityonion.net/training
Security Onion Solutions Hardware Appliances
We know Security Onion's hardware needs, and our appliances are the perfect match for the platform. Leave the hardware research, testing, and support to us, so you can focus on what's important for your organization. Not only will you have confidence that your Security Onion deployment is running on the best-suited hardware, you will also be supporting future development and maintenance of the Security Onion project!
https://securityonionsolutions.com/hardware
Cloud Installations
For new Security Onion 2 installations in the cloud, Security Onion 2.4 will soon be available on the AWS, Azure, and GCP marketplaces!
AWS Marketplace and Documentation:
https://securityonion.net/aws/?ref=_ptnr_soc_blog_240529
https://docs.securityonion.net/en/2.4/cloud-amazon.html
Azure Marketplace and documentation:
https://securityonion.net/azure
https://docs.securityonion.net/en/2.4/cloud-azure.html
GCP Marketplace and documentation:
https://securityonion.net/google
https://docs.securityonion.net/en/2.4/cloud-google.html
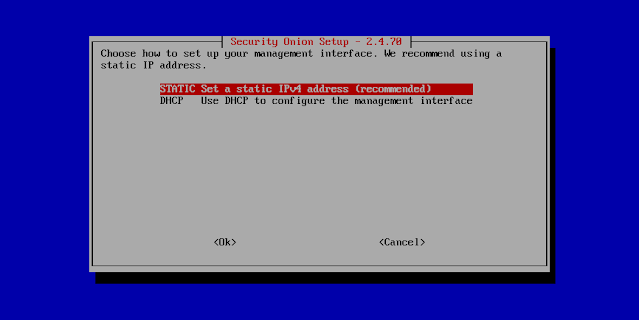
Screenshot Tour
If you want the quickest and easiest way to try out Security Onion 2.4, just follow the screenshots below to install an Import node. This can be done in a minimal VM with only 4GB RAM! For more information, please see:
https://docs.securityonion.net/en/2.4/first-time-users.html















































































































No comments:
Post a Comment