Security Onion 16.04.6.3 is now available!
 |
| Security Onion 16.04.6.3 |
Major Changes Since Last ISO Image
- Elastic 6.8.4
- CyberChef 9.11.7
- Bro 2.6.4
- Suricata 4.1.5
- Snort 2.9.15.0
Thanks
Thanks to Wes Lambert for testing this ISO image!
Package Updates
This release also includes the following updated packages:
pinguybuilder - 20180514-1ubuntu1securityonion20
This package resolves the following issue:
pinguybuilder: increment version to 16.04.6.3 #1668
https://github.com/Security-Onion-Solutions/security-onion/issues/1668
Issues Resolved
For a list of all issues resolved in this release, please see:
https://github.com/Security-Onion-Solutions/security-onion/projects/8
Release Notes
For more information about this release, please see:
https://securityonion.net/docs/release-notes.html
Installation Guide
We've updated the Installation guide to reflect the download locations for the new ISO image:
https://securityonion.net/docs/installation.html
Existing Deployments
If you have existing 16.04 installations, there is no need to download the new ISO image. You can simply continue using our standard update process to install updated packages as they are made available:
https://securityonion.net/docs/Upgrade
If you have existing installations of Security Onion 14.04, you can upgrade from 14.04 to 16.04:
https://securityonion.net/docs/upgrading-from-14.04-to-16.04.html
Documentation
We've got a new documentation site! Please let us know if anything needs to be updated:
https://securityonion.net/docs
Also, we're now offering a printed copy of our official documentation with foreword by Richard Bejtlich and proceeds going to Rural Technology Fund:
https://securityonion.net/book
Training
Security Onion Solutions is the only official authorized training provider for Security Onion and we have 4-day Basic and 4-day Advanced onsite training classes. We also offer online classes as well. For more information, please see:
https://securityonionsolutions.com
Appliances
We now offer hardware appliances! For more information, please see:
https://blog.securityonion.net/2018/10/introducing-security-onion-solutions.html
Support
Need support? Please see:
https://securityonion.net/docs/Support
Screenshot Tour
 |
| ISO Boot Menu |
 |
| Once the Live Desktop appears, double-click the Install icon and follow the prompts |
|
 |
| Once you've completed the installer and rebooted, login using the username and password you created in the installer |
|
 |
| After logging in, you are prompted to run Setup |
|
 |
| Setup can now run interactively via CLI and sosetup-minimal can be used to minimize RAM and CPU usage |
|
 |
| Configure network interfaces |
|
 |
| If your hostname is securityonion, Setup gives you the opportunity to rename it |
|
 |
| Configure your network interfaces, reboot, then log back in |
|
 |
| Launch Setup again and skip network configuration to go to service configuration |
|
 |
| sosetup-minimal can run Evaluation Mode in 4GB RAM |
|
 |
| Confirm sniffing interface |
|
 |
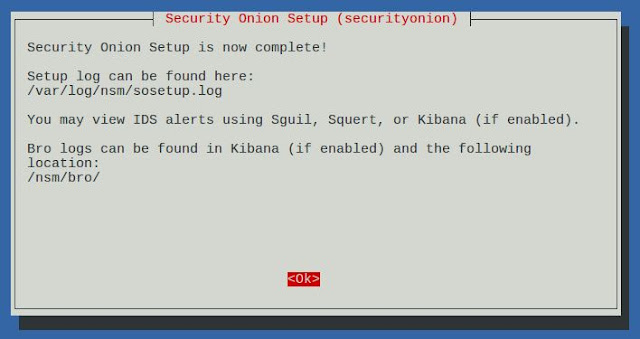
| Please wait while Setup configures your system |
|
 |
| Desktop no longer prompts to run Setup and includes icons for analyst applications |
|
 |
| The README shortcut includes links to the cheat sheet and online and offline documentation |
|
 |
| Single Sign On (SSO) for Squert, CapMe, and Kibana |
|
 |
| sosetup-minimal can run Evaluation Mode in only 4GB RAM |
|
 |
| Analyze IDS alerts using Squert |
|
 |
| Retrieve full packet capture with CapMe |
|
 |
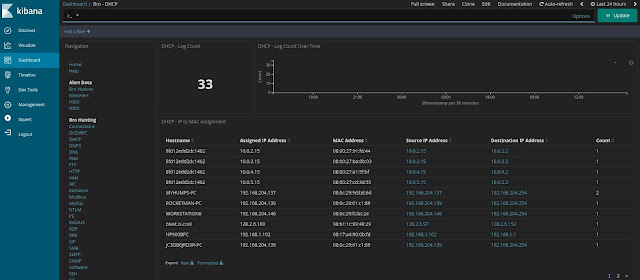
| Kibana Overview Dashboard |
|
 |
| Help |
 |
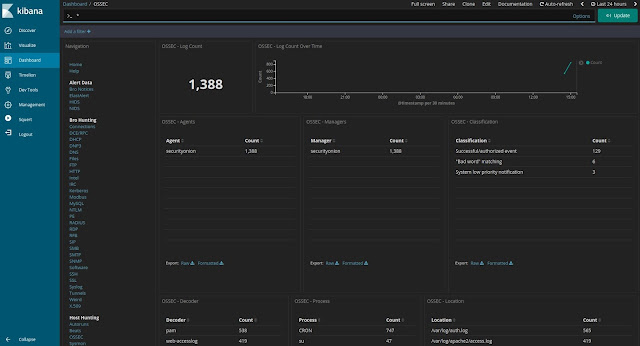
| HIDS Alerts from OSSEC/Wazuh |
|
 |
| NIDS Alerts from Snort or Suricata |
|