The following package is now available:
securityonion-sostat - 20120722-0ubuntu0securityonion90
This new package should resolve the following issue:
sostat: don't show queue stats if logstash not initialized #1214
https://github.com/Security-Onion-Solutions/security-onion/issues/1214
Thanks
Thanks to Wes Lambert for submitting the pull request and testing this new package!
Updating
Please see the following page for full update instructions:
https://securityonion.net/wiki/Upgrade
Training
We have a 4-day Security Onion training class coming up in San Antonio, Texas! For this and other training options, please see:
https://securityonionsolutions.com
Support
Need support? Please see:
https://securityonion.net/wiki/Support
Thanks!
Wednesday, February 28, 2018
Tuesday, February 27, 2018
CyberChef now included in Security Onion!
CyberChef is the "Cyber Swiss Army Knife - a web app for encryption, encoding, compression and data analysis":
https://github.com/gchq/CyberChef
The following package is now available:
securityonion-web-page - 20141015-0ubuntu0securityonion73
This new package should resolve the following issue:
Issue 1211: securityonion-web-page: add cyberchef
https://github.com/Security-Onion-Solutions/security-onion/issues/1211
Thanks
Thanks to the CyberChef team for CyberChef!
Thanks to Wes Lambert for testing this new package!
Updating
Please see the following page for full update instructions:
https://securityonion.net/wiki/Upgrade
Training
We have a 4-day Security Onion training class coming up in San Antonio, Texas! For this and other training options, please see:
https://securityonionsolutions.com
Support
Need support? Please see:
https://securityonion.net/wiki/Support
Thanks!
https://github.com/gchq/CyberChef
The following package is now available:
securityonion-web-page - 20141015-0ubuntu0securityonion73
This new package should resolve the following issue:
Issue 1211: securityonion-web-page: add cyberchef
https://github.com/Security-Onion-Solutions/security-onion/issues/1211
 |
| To access CyberChef, go to the main web page and click the CyberChef hyperlink |
 |
| CyberChef |
Thanks
Thanks to the CyberChef team for CyberChef!
Thanks to Wes Lambert for testing this new package!
Updating
Please see the following page for full update instructions:
https://securityonion.net/wiki/Upgrade
Training
We have a 4-day Security Onion training class coming up in San Antonio, Texas! For this and other training options, please see:
https://securityonionsolutions.com
Support
Need support? Please see:
https://securityonion.net/wiki/Support
Thanks!
Monday, February 26, 2018
Bro 2.5.3 now available for Security Onion!
Bro 2.5.3 was released recently:
http://blog.bro.org/2018/02/bro-253-released-security-update.html
https://www.bro.org/download/NEWS.bro.html
https://www.bro.org/download/CHANGES.bro.txt
The following packages are now available:
securityonion-bro - 2.5.3-1ubuntu1securityonion1
securityonion-bro-scripts - 20121004-0ubuntu0securityonion55
These new packages should resolve the following issues:
Bro 2.5.3 #1207
https://github.com/Security-Onion-Solutions/security-onion/issues/1207
Thanks
Thanks to the Bro team for Bro 2.5.3!
Thanks to Wes Lambert for testing these new packages!
Updating
Please see the following page for full update instructions:
https://securityonion.net/wiki/Upgrade
Training
We have a 4-day Security Onion training class coming up in San Antonio, Texas! For this and other training options, please see:
https://securityonionsolutions.com
Support
Need support? Please see:
https://securityonion.net/wiki/Support
Thanks!
http://blog.bro.org/2018/02/bro-253-released-security-update.html
https://www.bro.org/download/NEWS.bro.html
https://www.bro.org/download/CHANGES.bro.txt
The following packages are now available:
securityonion-bro - 2.5.3-1ubuntu1securityonion1
securityonion-bro-scripts - 20121004-0ubuntu0securityonion55
These new packages should resolve the following issues:
Bro 2.5.3 #1207
https://github.com/Security-Onion-Solutions/security-onion/issues/1207
Thanks
Thanks to the Bro team for Bro 2.5.3!
Thanks to Wes Lambert for testing these new packages!
Updating
Please see the following page for full update instructions:
https://securityonion.net/wiki/Upgrade
Training
We have a 4-day Security Onion training class coming up in San Antonio, Texas! For this and other training options, please see:
https://securityonionsolutions.com
Support
Need support? Please see:
https://securityonion.net/wiki/Support
Thanks!
Wednesday, February 21, 2018
securityonion-sostat - 20120722-0ubuntu0securityonion89 now available for Security Onion!
securityonion-sostat - 20120722-0ubuntu0securityonion89 is now available!
Issues Resolved
sostat: update logstash section since persistent queue is now disabled by default #1212
https://github.com/Security-Onion-Solutions/security-onion/issues/1212
Thanks
Thanks to Wes Lambert for updating sostat!
Updating
Please see the following page for full update instructions:
https://securityonion.net/wiki/Upgrade
Training
Security Onion Solutions offers onsite and online training! For more information, please see:
https://securityonionsolutions.com
Support
Need support? Please see:
https://securityonion.net/wiki/Support
Thanks!
Issues Resolved
sostat: update logstash section since persistent queue is now disabled by default #1212
https://github.com/Security-Onion-Solutions/security-onion/issues/1212
Thanks
Thanks to Wes Lambert for updating sostat!
Updating
Please see the following page for full update instructions:
https://securityonion.net/wiki/Upgrade
Training
Security Onion Solutions offers onsite and online training! For more information, please see:
https://securityonionsolutions.com
Support
Need support? Please see:
https://securityonion.net/wiki/Support
Thanks!
Tuesday, February 20, 2018
Security Onion Elastic Stack Release Candidate 2 and Security Onion 14.04.5.8 ISO Image!
UPDATED 2018/04/09! We've released a newer version!
https://blog.securityonion.net/2018/04/security-onion-elastic-stack-general.html
We're excited to announce that our Elastic Stack integration has now reached Release Candidate 2 (RC2)! RC2 includes a new 14.04.5.8 ISO image that contains these RC2 components and all the latest Ubuntu and Security Onion updates as of February 14, 2018!
RC2 Highlights
Major Changes in this release:
- All Ubuntu and Security Onion updates as of 2018/2/14
- Elastic Stack Release Candidate 2:
https://github.com/Security-Onion-Solutions/security-onion/issues/1198
- Docker images based on Elastic Stack 6.1.3
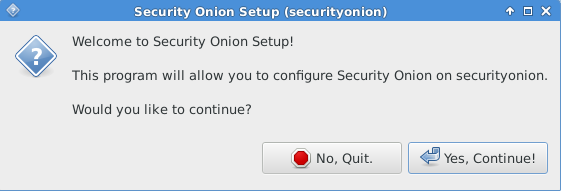
- Experimental Setup has been redesigned to add new options and make them easier to understand
- If choosing Production Mode, Setup will ask if you are building a new deployment or joining an existing one:
- If building a new deployment, Setup will ask if you want to store logs locally on the master server or output to separate load-balanced storage nodes:
- If joining an existing deployment, Setup will then ask what type of node you want to add - Forward, Heavy, or Storage:
- Forward Nodes generate and collect logs and forward them to the master server. Full packet capture remains on Forward Nodes. They do not run any Elastic stack processes. Forward Nodes require less hardware than Heavy Nodes, but typically use more network bandwidth.
- Heavy Nodes generate and collect logs and store them locally (similar to traditional ELSA sensors). Heavy Nodes run Elasticsearch and Logstash and the master server queries Heavy Nodes via cross cluster search. Heavy Nodes require more hardware than Forward Nodes, but typically use less network bandwidth.
- Storage Nodes do not generate logs themselves but simply extend the storage of the master server. They require that the master server has already been configured to load balance to additional storage nodes via redis. Storage Nodes run Elasticsearch and Logstash. The master server queries storage nodes via cross cluster search.
- so-elastic-start-logstash checks for LOGSTASH_OUTPUT_REDIS=yes in /etc/nsm/securityonion.conf and, if set, will automatically start redis and configure Logstash to output to it. So if you build a master server and initially choose to store logs locally, you can later convert it to redis output by setting LOGSTASH_OUTPUT_REDIS="yes" in /etc/nsm/securityonion.conf and then restarting Logstash:
- Logstash parsers have been updated to detect Bro logs in JSON and parse as such, otherwise fall back to csv or grok where appropriate
- Bro logs now write Bro timestamp to `@timestamp` field (Logstash timestamp can now be found in `timestamp`)
- New so-autossh-* scripts control the autossh tunnel that connects nodes to master server
- On nodes where Elasticsearch is enabled, curator should be fully configured to close indices after 30 days (see /etc/curator/ and /etc/cron.d/curator-close)
- Kibana - Management - Index Patterns should show the following Index Patterns (no more duplicates):
curl http://localhost:9200/_cat/indices
- so-migrate-elsa-to-elastic has been renamed to so-elsa-export and just exports data without automatically importing to Logstash
- Lots of other improvements and bug fixes!
Issues Resolved
Issue 1198: Elastic Stack Release Candidate 2
https://github.com/Security-Onion-Solutions/security-onion/issues/1198
Issue 1199: 14.04.5.8 ISO image
https://github.com/Security-Onion-Solutions/security-onion/issues/1199
This new ISO image has been tested by Wes Lambert, Audrius J, and Jay Hawk. Thanks, all!
Known Issues
If you start with Bro logs in JSON and then revert back to TSV format, some fields may conflict which may result in logs no longer loading properly. This will be resolved in RC3. We recommend most folks keep Bro logs in JSON format for better performance.
If you refresh the field list in Kibana, you may see a conflict for the timestamp or other fields and this may result in logging or dashboard issues. This will be resolved in RC3. We recommend that you avoid refreshing the field list unless absolutely necessary.
For other known issues, please see the todo list for our next release:
https://github.com/Security-Onion-Solutions/security-onion/issues/1208
Thanks
Special thanks to the following for their contributions to our Elastic Stack integration!
New Installations
We've updated the Verify_ISO page for the new ISO image:
https://github.com/Security-Onion-Solutions/security-onion/blob/master/Verify_ISO.md
Please remember to verify the signature of the downloaded ISO image using the instructions on that page.
Please note! This ISO image includes the EXPERIMENTAL Elastic stack!
The Elastic components are included in the ISO image and Setup gives you an option of Stable Setup (ELSA) or Experimental Setup (Elastic). If you do not want to try the new Elastic stack, you can choose Stable Setup. If you choose Experimental Setup, the usual disclaimers and warnings apply!
For more about Elastic Release Candidate 2, please see https://securityonion.net/wiki/elastic and the Screenshot tour at the bottom of this blog post.
Please note the following minimum hardware requirements for the Elastic stack:
If you would prefer an ISO image with no Elastic components at all, you have a few options:
OR
Existing Deployments
If you have existing ELSA installations based on a previous 14.04 ISO image, there is no need to download this new ISO image. You can simply continue using our standard update process to install updated packages as they are made available:
https://github.com/Security-Onion-Solutions/security-onion/wiki/Upgrade
If you have existing Elastic installations (Technology Previews, Alpha, Beta, or RC1), we don't officially support upgrading to newer releases, but you can try the steps listed here:
https://securityonion.net/wiki/elastic-rc2
Release Notes
For more information about this release, please see:
https://github.com/Security-Onion-Solutions/security-onion/wiki/Security-Onion-14.04-Release-Notes
Feedback
We want to hear from you! What works well? What could be improved? Please send feedback to our mailing list and include "Elastic RC2" in the Subject:
https://github.com/Security-Onion-Solutions/security-onion/wiki/MailingLists
Previous Releases
To see our progress over the last few months, please see the previous announcements:
http://blog.securityonion.net/2017/03/towards-elk-on-security-onion.html
http://blog.securityonion.net/2017/06/towards-elastic-on-security-onion.html
http://blog.securityonion.net/2017/07/towards-elastic-on-security-onion.html
http://blog.securityonion.net/2017/09/elastic-stack-alpha-release-and.html
http://blog.securityonion.net/2017/11/elastic-stack-beta-release-and-security.html
http://blog.securityonion.net/2017/11/elastic-stack-beta-2-release-and.html
http://blog.securityonion.net/2017/12/security-onion-elastic-stack-beta-3.html
http://blog.securityonion.net/2018/01/security-onion-elastic-stack-release.html
Training
We offer onsite and online training! For more information, please see:
https://securityonionsolutions.com
Support
Need support? Please see:
https://securityonion.net/wiki/Support
Screenshot Tour
https://blog.securityonion.net/2018/04/security-onion-elastic-stack-general.html
RC2 Highlights
Major Changes in this release:
- All Ubuntu and Security Onion updates as of 2018/2/14
- Elastic Stack Release Candidate 2:
https://github.com/Security-Onion-Solutions/security-onion/issues/1198
- Docker images based on Elastic Stack 6.1.3
- Experimental Setup has been redesigned to add new options and make them easier to understand
- If choosing Production Mode, Setup will ask if you are building a new deployment or joining an existing one:
- If building a new deployment, Setup will ask if you want to store logs locally on the master server or output to separate load-balanced storage nodes:
- If joining an existing deployment, Setup will then ask what type of node you want to add - Forward, Heavy, or Storage:
- Forward Nodes generate and collect logs and forward them to the master server. Full packet capture remains on Forward Nodes. They do not run any Elastic stack processes. Forward Nodes require less hardware than Heavy Nodes, but typically use more network bandwidth.
- Heavy Nodes generate and collect logs and store them locally (similar to traditional ELSA sensors). Heavy Nodes run Elasticsearch and Logstash and the master server queries Heavy Nodes via cross cluster search. Heavy Nodes require more hardware than Forward Nodes, but typically use less network bandwidth.
- Storage Nodes do not generate logs themselves but simply extend the storage of the master server. They require that the master server has already been configured to load balance to additional storage nodes via redis. Storage Nodes run Elasticsearch and Logstash. The master server queries storage nodes via cross cluster search.
- so-elastic-start-logstash checks for LOGSTASH_OUTPUT_REDIS=yes in /etc/nsm/securityonion.conf and, if set, will automatically start redis and configure Logstash to output to it. So if you build a master server and initially choose to store logs locally, you can later convert it to redis output by setting LOGSTASH_OUTPUT_REDIS="yes" in /etc/nsm/securityonion.conf and then restarting Logstash:
sudo docker stop so-logstash- so-elastic-configure now configures Bro to output in JSON
sudo docker rm so-logstash
sudo so-elastic-start-logstash
- Logstash parsers have been updated to detect Bro logs in JSON and parse as such, otherwise fall back to csv or grok where appropriate
- Bro logs now write Bro timestamp to `@timestamp` field (Logstash timestamp can now be found in `timestamp`)
- New so-autossh-* scripts control the autossh tunnel that connects nodes to master server
- On nodes where Elasticsearch is enabled, curator should be fully configured to close indices after 30 days (see /etc/curator/ and /etc/cron.d/curator-close)
- Kibana - Management - Index Patterns should show the following Index Patterns (no more duplicates):
*:logstash-*- Replicas now disabled properly for all Elasticsearch indices so all indices should show as GREEN:
*:elastalert_status*
*:logstash-beats-*
curl http://localhost:9200/_cat/indices
- so-migrate-elsa-to-elastic has been renamed to so-elsa-export and just exports data without automatically importing to Logstash
- Lots of other improvements and bug fixes!
Issues Resolved
Issue 1198: Elastic Stack Release Candidate 2
https://github.com/Security-Onion-Solutions/security-onion/issues/1198
https://github.com/Security-Onion-Solutions/security-onion/issues/1199
This new ISO image has been tested by Wes Lambert, Audrius J, and Jay Hawk. Thanks, all!
Known Issues
If you start with Bro logs in JSON and then revert back to TSV format, some fields may conflict which may result in logs no longer loading properly. This will be resolved in RC3. We recommend most folks keep Bro logs in JSON format for better performance.
If you refresh the field list in Kibana, you may see a conflict for the timestamp or other fields and this may result in logging or dashboard issues. This will be resolved in RC3. We recommend that you avoid refreshing the field list unless absolutely necessary.
For other known issues, please see the todo list for our next release:
https://github.com/Security-Onion-Solutions/security-onion/issues/1208
Thanks
Special thanks to the following for their contributions to our Elastic Stack integration!
- Elastic.co
- Justin Henderson
- Mark Baggett
New Installations
We've updated the Verify_ISO page for the new ISO image:
https://github.com/Security-Onion-Solutions/security-onion/blob/master/Verify_ISO.md
Please remember to verify the signature of the downloaded ISO image using the instructions on that page.
Please note! This ISO image includes the EXPERIMENTAL Elastic stack!
The Elastic components are included in the ISO image and Setup gives you an option of Stable Setup (ELSA) or Experimental Setup (Elastic). If you do not want to try the new Elastic stack, you can choose Stable Setup. If you choose Experimental Setup, the usual disclaimers and warnings apply!
- Experimental Setup is BLEEDING EDGE and TOTALLY UNSUPPORTED!
- If this breaks your system, you get to keep both pieces!
- This is a work in progress and is in constant flux.
- This is intended to build a quick prototype proof of concept so you can see what our ultimate Elastic configuration might look like. This configuration will change drastically over time leading up to the final release.
- Do NOT run this on a system that you care about!
- Do NOT run this on a system that has data that you care about!
- This should only be run on a TEST box with TEST data!
- Experimental Setup may result in nausea, vomiting, or a burning sensation.
For more about Elastic Release Candidate 2, please see https://securityonion.net/wiki/elastic and the Screenshot tour at the bottom of this blog post.
Please note the following minimum hardware requirements for the Elastic stack:
- 2 CPU cores
- 8GB RAM
If you would prefer an ISO image with no Elastic components at all, you have a few options:
- Install the older Security Onion 14.04.5.2 ISO image and then run "sudo soup"
OR
- Install your preferred flavor of Ubuntu 14.04 and then add our PPA and your desired packages:
https://github.com/Security-Onion-Solutions/security-onion/wiki/InstallingOnUbuntu
Existing Deployments
If you have existing ELSA installations based on a previous 14.04 ISO image, there is no need to download this new ISO image. You can simply continue using our standard update process to install updated packages as they are made available:
https://github.com/Security-Onion-Solutions/security-onion/wiki/Upgrade
If you have existing Elastic installations (Technology Previews, Alpha, Beta, or RC1), we don't officially support upgrading to newer releases, but you can try the steps listed here:
https://securityonion.net/wiki/elastic-rc2
Release Notes
For more information about this release, please see:
https://github.com/Security-Onion-Solutions/security-onion/wiki/Security-Onion-14.04-Release-Notes
Feedback
We want to hear from you! What works well? What could be improved? Please send feedback to our mailing list and include "Elastic RC2" in the Subject:
https://github.com/Security-Onion-Solutions/security-onion/wiki/MailingLists
Previous Releases
To see our progress over the last few months, please see the previous announcements:
http://blog.securityonion.net/2017/03/towards-elk-on-security-onion.html
http://blog.securityonion.net/2017/06/towards-elastic-on-security-onion.html
http://blog.securityonion.net/2017/07/towards-elastic-on-security-onion.html
http://blog.securityonion.net/2017/09/elastic-stack-alpha-release-and.html
http://blog.securityonion.net/2017/11/elastic-stack-beta-release-and-security.html
http://blog.securityonion.net/2017/11/elastic-stack-beta-2-release-and.html
http://blog.securityonion.net/2017/12/security-onion-elastic-stack-beta-3.html
http://blog.securityonion.net/2018/01/security-onion-elastic-stack-release.html
Training
We offer onsite and online training! For more information, please see:
https://securityonionsolutions.com
Support
Need support? Please see:
https://securityonion.net/wiki/Support
Screenshot Tour
 |
| Security Onion 14.04.5.8 20180214 |
 |
| Welcome to Setup |
 |
| Network Configuration |
 |
| Stable Setup (ELSA) vs Experimental Setup (Elastic) |
 |
| Elastic Setup |
 |
| Evaluation Mode vs Production Mode |
 |
| Monitor (Sniffing) Interface Selection |
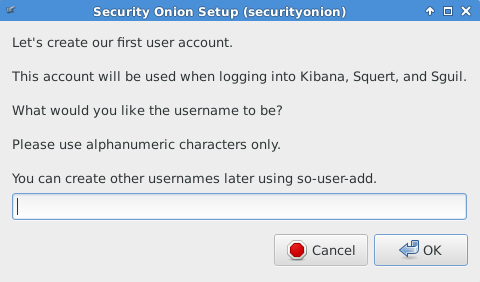 |
| Creating First User Account |
 |
| Creating Password |
 |
| Confirming Password |
 |
| Confirming Options |
 |
| Setup Complete |
 |
| Single Sign On (SSO) for Squert, CapMe, and Kibana |
 |
| Squert |
 |
| CapMe |
 |
| Kibana Home (Overview) Dashboard |
 |
| Help |
 |
| Bro Notices |
 |
| ElastAlert |
 |
| OSSEC HIDS Alerts |
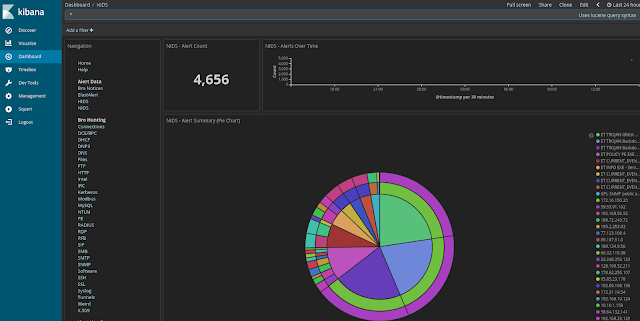 |
| NIDS Alerts from Snort or Suricata |
 |
| Bro - Connections |
 |
| Bro - DCE/RPC |
 |
| Bro - DHCP |
 |
| Bro - DNP3 |
 |
| Bro - DNS |
 |
| Bro - Files |
 |
| Bro - FTP |
 |
| Bro - HTTP |
 |
| Bro - Intel |
 |
| Bro - IRC |
 |
| Bro - Kerberos |
 |
| Bro - Modbus |
 |
| Bro - MySQL |
 |
| Bro - NTLM |
 |
| Bro - PE |
 |
| Bro - RADIUS |
 |
| Bro - RDP |
 |
| Bro - RFB |
 |
| Bro - SIP |
 |
| Bro - SMB |
 |
| Bro - SMTP |
 |
| Bro - SNMP |
 |
| Bro - Software |
 |
| Bro - SSH |
 |
| Bro - SSL |
 |
| Bro - Syslog |
 |
| Bro - Tunnels |
 |
| Bro - Weird |
 |
| Bro - X.509 |
 |
| Autoruns |
 |
| Beats |
 |
| OSSEC Logs |
 |
| Sysmon |
 |
| Domain Stats |
 |
| Firewall |
 |
| Frequency Analysis |
 |
| Stats |
 |
| Syslog |
Subscribe to:
Posts (Atom)
Search This Blog
Featured Post
Security Onion 3.1.0 Hotfix 20260528 Now Available!
Last week, we released Security Onion 3.1.0: https://blog.securityonion.net/2026/05/security-onion-310-now-available-with.html Today we are ...
Popular Posts
-
Security Onion 2.4.160 is now available and includes Playbooks and Guided Analysis to help you more quickly triage and respond to alerts! Se...
-
Security Onion 3.0.0 is now available and includes a new and improved interface, updated components, and many quality of life improvements! ...
-
Security Onion 2.4.180 is now available and includes several new features, updated components, and many quality of life improvements! For Se...
Blog Archive
- May 2026 (6)
- April 2026 (4)
- March 2026 (5)
- January 2026 (3)
- December 2025 (5)
- November 2025 (2)
- October 2025 (2)
- September 2025 (3)
- August 2025 (4)
- July 2025 (3)
- June 2025 (3)
- May 2025 (5)
- April 2025 (2)
- March 2025 (7)
- February 2025 (5)
- January 2025 (11)
- December 2024 (3)
- November 2024 (1)
- October 2024 (9)
- September 2024 (16)
- August 2024 (3)
- July 2024 (7)
- June 2024 (5)
- May 2024 (2)
- April 2024 (7)
- March 2024 (5)
- February 2024 (3)
- January 2024 (3)
- December 2023 (15)
- November 2023 (27)
- October 2023 (18)
- September 2023 (3)
- August 2023 (8)
- July 2023 (4)
- June 2023 (3)
- May 2023 (2)
- April 2023 (4)
- March 2023 (4)
- February 2023 (5)
- January 2023 (3)
- December 2022 (5)
- November 2022 (2)
- October 2022 (9)
- September 2022 (3)
- August 2022 (8)
- July 2022 (7)
- June 2022 (9)
- May 2022 (14)
- April 2022 (7)
- March 2022 (6)
- February 2022 (11)
- January 2022 (12)
- December 2021 (19)
- November 2021 (25)
- October 2021 (22)
- September 2021 (23)
- August 2021 (30)
- July 2021 (13)
- June 2021 (4)
- May 2021 (3)
- April 2021 (4)
- March 2021 (7)
- February 2021 (5)
- January 2021 (4)
- December 2020 (13)
- November 2020 (5)
- October 2020 (12)
- September 2020 (3)
- August 2020 (6)
- July 2020 (8)
- June 2020 (5)
- May 2020 (9)
- April 2020 (11)
- March 2020 (7)
- February 2020 (4)
- January 2020 (1)
- December 2019 (6)
- November 2019 (4)
- October 2019 (8)
- September 2019 (7)
- August 2019 (7)
- July 2019 (4)
- June 2019 (7)
- May 2019 (20)
- April 2019 (8)
- March 2019 (7)
- February 2019 (7)
- January 2019 (12)
- December 2018 (12)
- November 2018 (13)
- October 2018 (10)
- September 2018 (4)
- August 2018 (16)
- July 2018 (11)
- June 2018 (13)
- May 2018 (4)
- April 2018 (11)
- March 2018 (9)
- February 2018 (10)
- January 2018 (9)
- December 2017 (7)
- November 2017 (7)
- October 2017 (9)
- September 2017 (4)
- August 2017 (7)
- July 2017 (5)
- June 2017 (8)
- May 2017 (4)
- April 2017 (2)
- March 2017 (1)
- February 2017 (3)
- January 2017 (15)
- December 2016 (9)
- November 2016 (3)
- October 2016 (5)
- September 2016 (13)
- August 2016 (12)
- July 2016 (10)
- June 2016 (7)
- May 2016 (7)
- April 2016 (7)
- March 2016 (10)
- February 2016 (13)
- January 2016 (10)
- December 2015 (1)
- November 2015 (1)
- October 2015 (3)
- September 2015 (5)
- August 2015 (7)
- July 2015 (7)
- June 2015 (12)
- May 2015 (6)
- April 2015 (6)
- March 2015 (6)
- February 2015 (10)
- January 2015 (11)
- December 2014 (5)
- November 2014 (3)
- October 2014 (6)
- September 2014 (20)
- August 2014 (7)
- July 2014 (10)
- June 2014 (10)
- May 2014 (3)
- April 2014 (9)
- March 2014 (6)
- February 2014 (9)
- January 2014 (8)
- December 2013 (5)
- November 2013 (2)
- October 2013 (7)
- September 2013 (5)
- August 2013 (7)
- July 2013 (9)
- June 2013 (7)
- May 2013 (11)
- April 2013 (3)
- March 2013 (3)
- February 2013 (3)
- January 2013 (3)
- December 2012 (3)
- November 2012 (1)
- October 2012 (1)
- September 2012 (1)
- August 2012 (2)
- May 2012 (4)
- April 2012 (6)
- March 2012 (8)
- February 2012 (4)
- January 2012 (13)
- December 2011 (9)
- November 2011 (8)
- October 2011 (8)
- September 2011 (8)
- July 2011 (4)
- June 2011 (5)
- May 2011 (2)
- April 2011 (1)
- February 2011 (1)
- January 2011 (11)
- November 2010 (4)
- October 2010 (8)
- August 2010 (1)
- July 2010 (2)
- June 2010 (1)
- May 2010 (1)
- April 2010 (2)
- February 2010 (3)
- January 2010 (1)
- September 2009 (1)
- August 2009 (3)
- July 2009 (4)
- June 2009 (3)
- May 2009 (1)
- April 2009 (8)
- February 2009 (1)
- January 2009 (9)
- November 2008 (2)
- October 2008 (4)
- September 2008 (3)



