One of my SANS 503 Mentor students has started his own blog. Check it out at:
http://detroitdavesraves.blogspot.com/
Thursday, April 23, 2009
Friday, April 17, 2009
How a Single Piece of Paper Can Saturate a WAN Link
At work, one of our remote business units was experiencing slowness in their WAN link. Our Network Architect began looking into the problem and found that one particular device on their network was sending enormous amounts of traffic over the link. Looking into it further, he discovered that the device was one of our security cameras in the business unit's server room. He then came to see us and asked about the camera.
This particular camera is motion-activated and therefore shouldn't have been capturing all the time, but it was. We looked at some of the videos and, at first, didn't see anything out of the ordinary. After racking our brains for a few minutes, we finally noticed that there was a piece of paper taped to the front of one of the server racks. The paper was taped in the middle, allowing the sides to flap in the wind of the air conditioner. This created just enough motion to trigger the camera to record and transmit its video.
All of this resulted in a call to the technician at the business unit that went something like this:
This particular camera is motion-activated and therefore shouldn't have been capturing all the time, but it was. We looked at some of the videos and, at first, didn't see anything out of the ordinary. After racking our brains for a few minutes, we finally noticed that there was a piece of paper taped to the front of one of the server racks. The paper was taped in the middle, allowing the sides to flap in the wind of the air conditioner. This created just enough motion to trigger the camera to record and transmit its video.
All of this resulted in a call to the technician at the business unit that went something like this:
"We've discovered the problem with your WAN link. Please go to your server room and remove the piece of paper taped to the front of the server rack. Your WAN link should then magically speed up. Thank you."My modest proposal is that paper is obviously increasing our bandwidth costs and we should therefore go completely paperless.
Wednesday, April 15, 2009
SANS GCIA Gold Paper on Snort 3.0 Beta 3
My SANS GCIA Gold Paper on Snort 3.0 Beta 3 has been posted to the SANS Reading Room!
Friday, April 10, 2009
Wireshark 1.0.7 is out!
Wireshark 1.0.7 has been released. Please upgrade ASAP! For more information about the release, please see:
http://www.wireshark.org/docs/relnotes/wireshark-1.0.7.html
http://www.wireshark.org/docs/relnotes/wireshark-1.0.7.html
Snort 2.8.4 is out!
Snort 2.8.4 has been released. From http://www.snort.org/pub-bin/snortnews.cgi#864:
http://www.snort.org/vrt/advisories/vrt-rules-2009-04-08.html
Snort 2.8.4 is now available on snort.org, at http://www.snort.org/dl/For more information about the new DCERPC rules, please see:
Snort 2.8.4 introduces:
- A revised DCE/RPC preprocessor with more rule options
With the new DCE/RPC preprocessor, there will be a number of updates to the rules. Please be sure to update your rules to the latest when that package is available (next few days).
- Support for IPv6 in Frag3 and all application preprocessors
- Improved target-based support in preprocessors
- Option to automatically pre-filter traffic that is not inspected in order to improve performance
- Several other improvements and fixes
Please see the release notes and changelog for more details.
Please submit bugs, questions, and feedback to bugs@snort.org.
Happy Snorting!
The Snort Release Team
http://www.snort.org/vrt/advisories/vrt-rules-2009-04-08.html
Monday, April 6, 2009
Snort 3.0 (SnortSP) Beta 3 -- Inline Bridging Mode in 3 Steps
To complete the updating of my 3-part series on Installing and Configuring Snort 3 Beta 3, I now present to you the final chapter in this trilogy: the updated recipe for Snort 3 Inline Bridging Mode in 3 Steps. Snort 3.0 Beta 3 has changed the syntax for creating a new dsrc, so this has been reflected in the new recipe.
Step 1: Add a new function to your snort.lua file
If you followed the updated Snort 3.0 Beta 3 Installation HOWTO, then the default snort.lua file is in /etc/snortsp/snort.lua. Open the file and add the following function:
Step 2: Start SnortSP
Start SnortSP using the following command:
Step 3: Use the bridge() function
In the Lua shell, type the following (replacing eth0 and eth1 with the correct interfaces on your system):
Once the bridge is up and running, you can do the following to display packets traversing the bridge:
When finished, shut down SnortSP by running the following command:
Step 1: Add a new function to your snort.lua file
If you followed the updated Snort 3.0 Beta 3 Installation HOWTO, then the default snort.lua file is in /etc/snortsp/snort.lua. Open the file and add the following function:
function bridge (interface1, interface2)
if interface2 == nil then
error("Two interface strings must be specified ( e.g. bridge(\"eth0\", \"eth1\") )")
end
dsrc1 = {name="src1",
type="afpacket",
intf=interface1..":"..interface2,
flags=10,
snaplen=1514,
display="none",
tcp={maxflows=262144, maxidle=30, flow_memcap=10000000},
other={maxflows=131072, maxidle=30, flow_memcap=1000000},
cksum_mode=0x0,
}
dsrc.new(dsrc1)
eng.new({name="e1"})
eng.link({engine="e1", source="src1"})
eng.start("e1")
end
Step 2: Start SnortSP
Start SnortSP using the following command:
sudo snortsp -L /etc/snortsp/snort.luaSnortSP will start up and read your new snort.lua file. You will then be greeted by the SnortSP Lua shell.
Step 3: Use the bridge() function
In the Lua shell, type the following (replacing eth0 and eth1 with the correct interfaces on your system):
bridge("eth0", "eth1")
Once the bridge is up and running, you can do the following to display packets traversing the bridge:
eng.set_display({engine="e1", display="none"})
Press the Up arrow and change "none" to "classic".
View the output.
Press the Up arrow twice to retrieve the "none" command and press Enter.
When finished, shut down SnortSP by running the following command:
ssp.shutdown()
Sunday, April 5, 2009
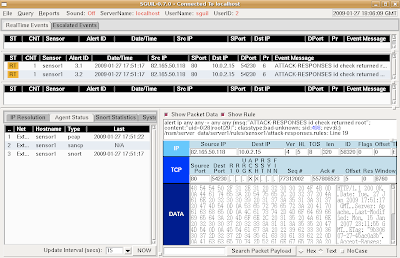
Integrating Snort 3.0 Beta 3 and Sguil in 3 Steps
Since I updated the "Installing Snort 3.0 Beta on Ubuntu 8.04" post to work with Snort 3.0 Beta 3, here's the update for the "Integrating Snort 3.0 (SnortSP) and Sguil in 3 Steps" post. Since the original post, NSMnow 1.3.5 has been released, so the URL has been updated in the recipe to reflect this new version. Also, there appears to be a bug in the current sspiffy.sh whereby it configures the dsrc type to be "file" instead of "pcap". I added a quick one-liner to correct this in the snort.lua file.
Please note that if you have an existing NSMnow installation, following this recipe may or may not work. This recipe is designed for new NSMnow installations.
The best open source tool to manage Snort alerts is Sguil and the easiest way to install Sguil is using NSMnow. NSMnow automatically installs and configures barnyard2 (compatible with SnortSP's unfied2 format), sancp, Sguil, and Snort 2.x. We're going to replace NSMnow's snort alert process with Snort 3.0.
This quick recipe assumes that you're running on Ubuntu 8.04 and your primary network interface is eth0. You should be able to copy/paste each of the three code blocks into your terminal.
Obligatory disclaimer: I offer no warranty of any kind. If this breaks your box, you get to keep both pieces.
Step 1: Get root privileges
Launch the Sguil client by opening a new terminal and typing the following:
Username: sguil
Password: password
Next, create some alerts by opening a browser and going to:
http://www.testmyids.com
Finally, go into the Sguil console and you should see two new alerts:
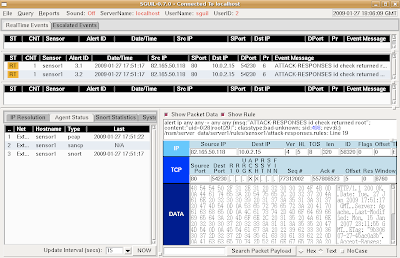
This demonstrates that SnortSP is capturing packets, analyzing them with the Snort 2.8.2 Detection Engine, and outputting in unified2 format, which is then read by Barnyard2 and inserted into the Sguil database.
When finished, return to your SnortSP window and press ctrl-c to terminate the SnortSP process. Then type "nsm --all --stop" to terminate all NSMnow processes.
Please note that if you have an existing NSMnow installation, following this recipe may or may not work. This recipe is designed for new NSMnow installations.
The best open source tool to manage Snort alerts is Sguil and the easiest way to install Sguil is using NSMnow. NSMnow automatically installs and configures barnyard2 (compatible with SnortSP's unfied2 format), sancp, Sguil, and Snort 2.x. We're going to replace NSMnow's snort alert process with Snort 3.0.
This quick recipe assumes that you're running on Ubuntu 8.04 and your primary network interface is eth0. You should be able to copy/paste each of the three code blocks into your terminal.
Obligatory disclaimer: I offer no warranty of any kind. If this breaks your box, you get to keep both pieces.
Step 1: Get root privileges
##########################Step 2: Install NSMnow
sudo -i
##########################
##########################Step 3: Configure NSMnow and SnortSP and start
mkdir /usr/local/src/NSMnow
cd /usr/local/src/NSMnow
wget http://www.securixlive.com/download/nsmnow/NSMnow-1.3.5.tar.gz
tar zxvf NSMnow-1.3.5.tar.gz
./NSMnow -i -y
##########################
##########################Snort 3.0 is now capturing packets on eth0 and analyzing them. Let's verify that now.
if ! grep "/nsm/server_data/server1/load" /etc/apparmor.d/usr.sbin.mysqld > /dev/null
then
sed -i 's|}| /nsm/server_data/server1/load/* r,|g' /etc/apparmor.d/usr.sbin.mysqld
echo "}" >> /etc/apparmor.d/usr.sbin.mysqld
fi
/etc/init.d/apparmor restart
/usr/local/sbin/nsm --server --start
/usr/local/sbin/nsm_sensor_ps-start --skip-snort-alert
mkdir /etc/snortsp_alert
cd /etc/snortsp_alert
cp -R /etc/nsm/sensor1/* .
mv snort.conf snort_orig.conf
sspiffy.sh /usr/local -c snort_orig.conf -i eth0
sed -i 's|type="file"|type="pcap"|g' snort.lua
grep -v "sameip" rules/bad-traffic.rules > rules/bad-traffic.rules.2
rm -f rules/bad-traffic.rules
mv rules/bad-traffic.rules.2 rules/bad-traffic.rules
snortsp -C -L snort.lua
##########################
Launch the Sguil client by opening a new terminal and typing the following:
##########################When prompted, login to Sguil using the default credentials:
sguil.tk
##########################
Username: sguil
Password: password
Next, create some alerts by opening a browser and going to:
http://www.testmyids.com
Finally, go into the Sguil console and you should see two new alerts:
This demonstrates that SnortSP is capturing packets, analyzing them with the Snort 2.8.2 Detection Engine, and outputting in unified2 format, which is then read by Barnyard2 and inserted into the Sguil database.
When finished, return to your SnortSP window and press ctrl-c to terminate the SnortSP process. Then type "nsm --all --stop" to terminate all NSMnow processes.
Saturday, April 4, 2009
Installing Snort 3.0 (SnortSP) Beta 3 on Ubuntu 8.04 in 3 Steps
Snort 3.0 Beta 3 was released on April 1. You can read an overview of the changes in Snort 3.0 Beta 3 in the mailing list announcement. For more details on the underlying architectural changes in Beta 3, see Marty Roesch's blog. Thanks to Marty and the rest of the Snort 3 Development Team for their hard work in this release!
Installing Snort 3.0 Beta 3 on Ubuntu 8.04 is almost identical to installing Snort 3.0 Beta 2 on Ubuntu 8.04. However, I did have an issue with the Snort 2.8 Detection Engine not compiling correctly. This turned out to be libtool not liking the fact that /bin/sh was symlinked to /bin/dash instead of /bin/bash. The one-line fix was:
Here's the complete install recipe that worked for me:
Step 1: Get root privileges
Installing Snort 3.0 Beta 3 on Ubuntu 8.04 is almost identical to installing Snort 3.0 Beta 2 on Ubuntu 8.04. However, I did have an issue with the Snort 2.8 Detection Engine not compiling correctly. This turned out to be libtool not liking the fact that /bin/sh was symlinked to /bin/dash instead of /bin/bash. The one-line fix was:
rm /bin/sh && ln -s /bin/bash /bin/sh(Special thanks to Russ Combs of the SnortSP development team for his assistance with this issue.)
Here's the complete install recipe that worked for me:
Step 1: Get root privileges
##########################Step 2: Install dependencies
sudo -i
##########################
##########################Step 3: Download, compile, and install Snort 3.0 Beta 3
aptitude update
aptitude -y install build-essential \
libdumbnet1 libdumbnet-dev \
uuid uuid-dev \
libncurses5 libncurses5-dev \
libreadline5 libreadline5-dev \
libpcap0.8 libpcap0.8-dev \
libpcre3 libpcre3-dev \
liblua5.1-0 liblua5.1-0-dev \
flex bison
##########################
##########################
rm /bin/sh && ln -s /bin/bash /bin/sh
cd /usr/local/src/
wget http://dl.snort.org/snortsp/\
snortsp-3.0.0b3.tar.gz
tar zxvf snortsp-3.0.0b3.tar.gz
cd snortsp-3.0.0b3/
./configure
make
make install
mkdir /etc/snortsp/
cp etc/* /etc/snortsp/
cd src/analysis/snort/
./configure \
--with-platform-includes=/usr/local/include \
--with-platform-libraries=/usr/local/lib
make
make install
ldconfig
##########################
Subscribe to:
Posts (Atom)
Search This Blog
Featured Post
Security Onion 3.1.0 Hotfix 20260528 Now Available!
Last week, we released Security Onion 3.1.0: https://blog.securityonion.net/2026/05/security-onion-310-now-available-with.html Today we are ...
Popular Posts
-
Security Onion 2.4.160 is now available and includes Playbooks and Guided Analysis to help you more quickly triage and respond to alerts! Se...
-
Security Onion 3.0.0 is now available and includes a new and improved interface, updated components, and many quality of life improvements! ...
-
Security Onion 2.4.180 is now available and includes several new features, updated components, and many quality of life improvements! For Se...
Blog Archive
- May 2026 (6)
- April 2026 (4)
- March 2026 (5)
- January 2026 (3)
- December 2025 (5)
- November 2025 (2)
- October 2025 (2)
- September 2025 (3)
- August 2025 (4)
- July 2025 (3)
- June 2025 (3)
- May 2025 (5)
- April 2025 (2)
- March 2025 (7)
- February 2025 (5)
- January 2025 (11)
- December 2024 (3)
- November 2024 (1)
- October 2024 (9)
- September 2024 (16)
- August 2024 (3)
- July 2024 (7)
- June 2024 (5)
- May 2024 (2)
- April 2024 (7)
- March 2024 (5)
- February 2024 (3)
- January 2024 (3)
- December 2023 (15)
- November 2023 (27)
- October 2023 (18)
- September 2023 (3)
- August 2023 (8)
- July 2023 (4)
- June 2023 (3)
- May 2023 (2)
- April 2023 (4)
- March 2023 (4)
- February 2023 (5)
- January 2023 (3)
- December 2022 (5)
- November 2022 (2)
- October 2022 (9)
- September 2022 (3)
- August 2022 (8)
- July 2022 (7)
- June 2022 (9)
- May 2022 (14)
- April 2022 (7)
- March 2022 (6)
- February 2022 (11)
- January 2022 (12)
- December 2021 (19)
- November 2021 (25)
- October 2021 (22)
- September 2021 (23)
- August 2021 (30)
- July 2021 (13)
- June 2021 (4)
- May 2021 (3)
- April 2021 (4)
- March 2021 (7)
- February 2021 (5)
- January 2021 (4)
- December 2020 (13)
- November 2020 (5)
- October 2020 (12)
- September 2020 (3)
- August 2020 (6)
- July 2020 (8)
- June 2020 (5)
- May 2020 (9)
- April 2020 (11)
- March 2020 (7)
- February 2020 (4)
- January 2020 (1)
- December 2019 (6)
- November 2019 (4)
- October 2019 (8)
- September 2019 (7)
- August 2019 (7)
- July 2019 (4)
- June 2019 (7)
- May 2019 (20)
- April 2019 (8)
- March 2019 (7)
- February 2019 (7)
- January 2019 (12)
- December 2018 (12)
- November 2018 (13)
- October 2018 (10)
- September 2018 (4)
- August 2018 (16)
- July 2018 (11)
- June 2018 (13)
- May 2018 (4)
- April 2018 (11)
- March 2018 (9)
- February 2018 (10)
- January 2018 (9)
- December 2017 (7)
- November 2017 (7)
- October 2017 (9)
- September 2017 (4)
- August 2017 (7)
- July 2017 (5)
- June 2017 (8)
- May 2017 (4)
- April 2017 (2)
- March 2017 (1)
- February 2017 (3)
- January 2017 (15)
- December 2016 (9)
- November 2016 (3)
- October 2016 (5)
- September 2016 (13)
- August 2016 (12)
- July 2016 (10)
- June 2016 (7)
- May 2016 (7)
- April 2016 (7)
- March 2016 (10)
- February 2016 (13)
- January 2016 (10)
- December 2015 (1)
- November 2015 (1)
- October 2015 (3)
- September 2015 (5)
- August 2015 (7)
- July 2015 (7)
- June 2015 (12)
- May 2015 (6)
- April 2015 (6)
- March 2015 (6)
- February 2015 (10)
- January 2015 (11)
- December 2014 (5)
- November 2014 (3)
- October 2014 (6)
- September 2014 (20)
- August 2014 (7)
- July 2014 (10)
- June 2014 (10)
- May 2014 (3)
- April 2014 (9)
- March 2014 (6)
- February 2014 (9)
- January 2014 (8)
- December 2013 (5)
- November 2013 (2)
- October 2013 (7)
- September 2013 (5)
- August 2013 (7)
- July 2013 (9)
- June 2013 (7)
- May 2013 (11)
- April 2013 (3)
- March 2013 (3)
- February 2013 (3)
- January 2013 (3)
- December 2012 (3)
- November 2012 (1)
- October 2012 (1)
- September 2012 (1)
- August 2012 (2)
- May 2012 (4)
- April 2012 (6)
- March 2012 (8)
- February 2012 (4)
- January 2012 (13)
- December 2011 (9)
- November 2011 (8)
- October 2011 (8)
- September 2011 (8)
- July 2011 (4)
- June 2011 (5)
- May 2011 (2)
- April 2011 (1)
- February 2011 (1)
- January 2011 (11)
- November 2010 (4)
- October 2010 (8)
- August 2010 (1)
- July 2010 (2)
- June 2010 (1)
- May 2010 (1)
- April 2010 (2)
- February 2010 (3)
- January 2010 (1)
- September 2009 (1)
- August 2009 (3)
- July 2009 (4)
- June 2009 (3)
- May 2009 (1)
- April 2009 (8)
- February 2009 (1)
- January 2009 (9)
- November 2008 (2)
- October 2008 (4)
- September 2008 (3)